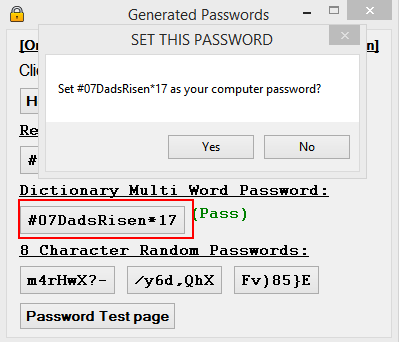
Multi word passwords. XKPasswd 2019-05-10
Common Words Random Password Creator
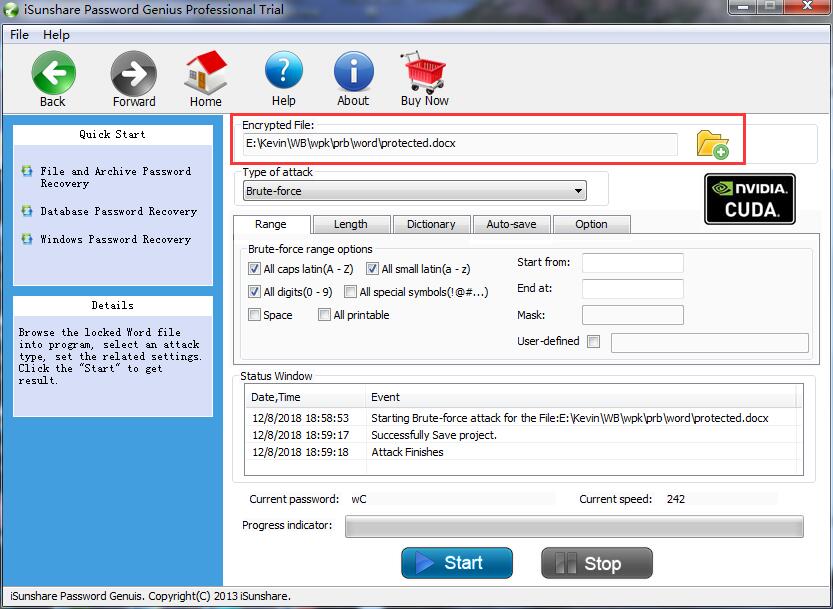
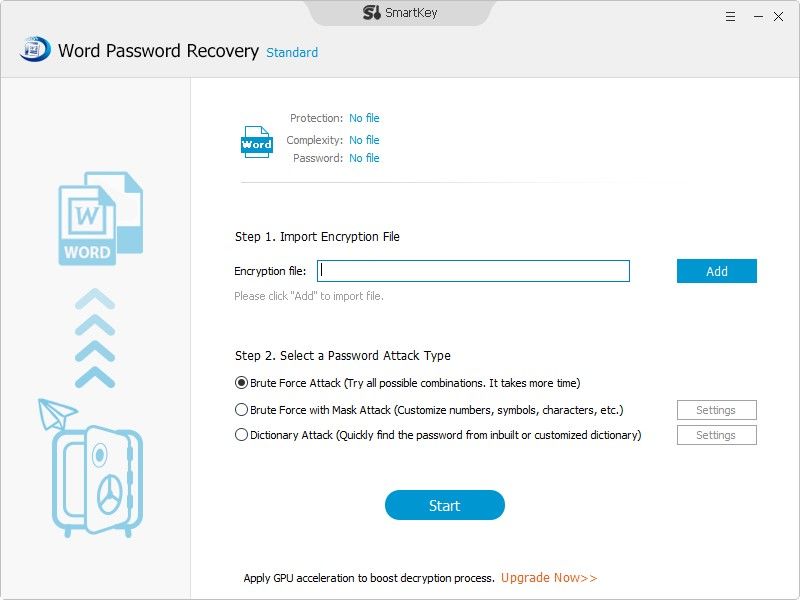
The only time such a situation applies is if you have, say, encrypted data and an adversary has gotten that data. There is no limitation on this. Both accounts end up getting compromised. It either applies the Brute-Force technique or uses the Office Password Remover to remove the password directly. Thank you for your cooperation. Suffice it to say that both options you gave are going to take a very long time to crack.
How safe are 'multi
August 10, 2016 Quickly lookup any person by e-mail address or name. The key to creating secure passwords is to make sure that the number of possible combinations is huge. While probably not quite as secure, LastPass offers two-factor authentication using Google Authenticator, so even if someone keylogs my pass-phrase they still won't be able to get my passwords without also getting access to my Android device which isn't a phone, so hacking it would be tricky too. This seemed like a nice way to support this website, but turned out to be far too much of a burden to our visitors. The maximum password length that can be recovered is 8 characters. It is impossible to conceive of a sane, logical approach to password management while limited by these arbitrary parameters. Store passwords inside this partition in something like KeePass.
Joel's Password Generator
The more characters a password cracking program has to crunch, the harder it is to guess. A wikipedia du There was a ship that tried using Vogon poetry for their password locks once. So, if movie names and slang is what many people are using as their pass-phrases, a dictionary attack is a little easier. So, eventually even if it's a massive brute force attack, it could still arrive at the one that worked. A much better way of thinking about it is guesses per dollar.
Common Words Random Password Creator
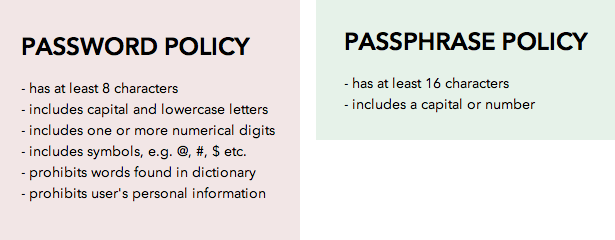
Most places will require a slew of different requisites for their passwords, from a minimum to a maximum length or both , whether you can have caps, symbols and how many and which symbols are permitted. As such their research is basically fucking worthless. All of this assumes you let a good quality, secure system do the password pick for you if you try to pick a password this way, you'll almost certainly get way less entropy. Do you have any tips on how to do that, or do you know of a script? Side effects of using passphrases like that include speaking random gibberish on occasion. The passphrase system they studied wouldn't allow duplicate passphrases.
4 Free Word Password Recovery Tools
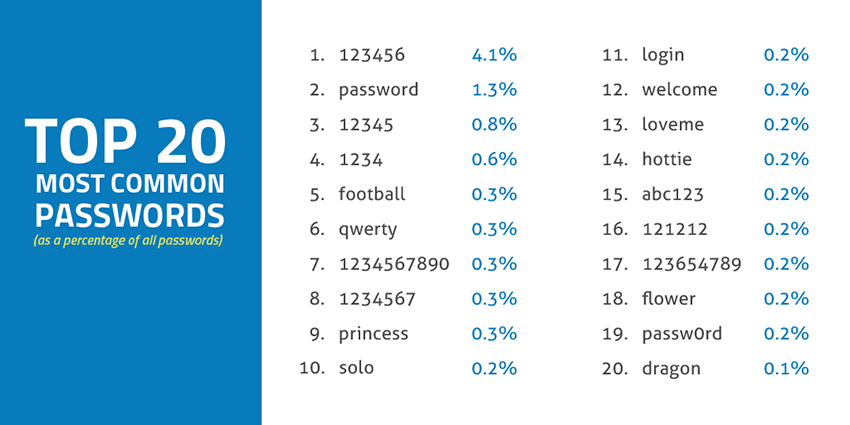
From a standard point, most of us only use a few password combinations for convenience, such as birthday, short names, pet name, etc. As an additional security measure, version 2. We already knew that people pick stupid passwords. My recommendation for a really secure pass phrase: 1. The paper suggests further collaboration between security and linguistics researchers. This happens quite often because there are so many passwords we need to remember in nowadays, such as lockscreen passcode, admin password, bank password, website password, etc… It's pretty easy to mess up the password if you didn't write them down.
Strong Random Password Generator

For me, is my favorite tool to restore forgotten password on office-based files, including Word, Excel and PowerPoint. As processors get faster, you simply increase the amount of work that you're asking for. This might be something that parents need to teach their children: Don't talk to strangers, brush your teeth everyday, and don't pick obvious passwords. It works if you use completely random words, but phrases are little better than using single dictionary words. Keep a good, long, easy-to-remember passphrase for access to your TrueCrypt partition that sits on a private computer inside your house.
What is a Password Cracker Program?
Take, for example, the on this issue. Despite the need to secure your files, mark that security issues is like a two sided coin. To a great extent, that's the point. Stats: This comic has been referenced 2220 times, representing 2. Take note of such limits to ensure your password is not being truncated. The examples below are passwords that the system will reject because they are methods commonly used on 'easy-to-guess' passwords. Except you can make a cipher practically impossible.
Word Password Recovery

My bank's website only allows letters and numbers for the password and only up to 20 characters, lame so I use a pattern on the keypad to remember it via muscle memory. November 23, 2013 Stand out; use special characters in your tweets or e-mails. Any word on its own is bad. If someone has a one in a million chance to determine my password how much of a threat is that to me if the site that requires the password only allows a few attempts before it locks the account? Brute forcing that is already more trouble than it's worth at three words, and five would r They don't, but if they have the resources for a brute-force search, it's moot since in theory they'll just keep trying until they find it. The 5 uncommon word password had a crack time of half a trillion years: after a 1000x speed, this becomes half a billion years. Stop thinking about the problem one dimensionally. My actual LastPass password the single point of failure is 32 characters long.
Strong Random Password Generator

This is a method that generates very strong password that are easier to memorize than random characters. Express recovery doesn't work with advanced encryption modes. Users are able to set parameters to exact range of password they need to search i. As far as I can tell from the documentation I've been reading, simply put a dictionary attack works by comparing the password hash against hashes generated from a word list with additional modifications such as o-0, 1-1 e-3 substitutions and casing changes. Of course, someone might start using that phrase berfore the rest stop using it.