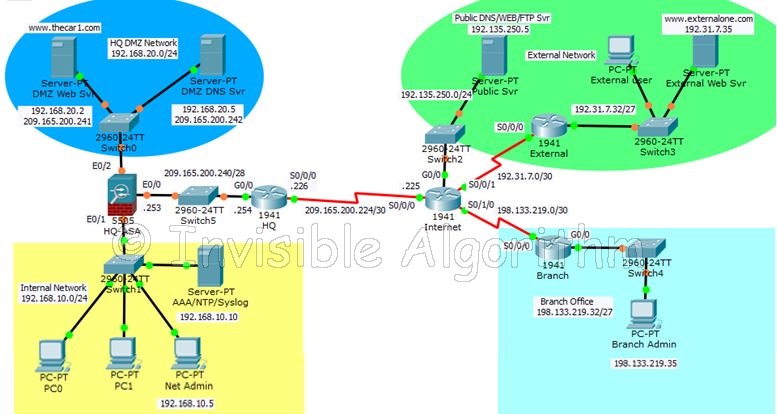
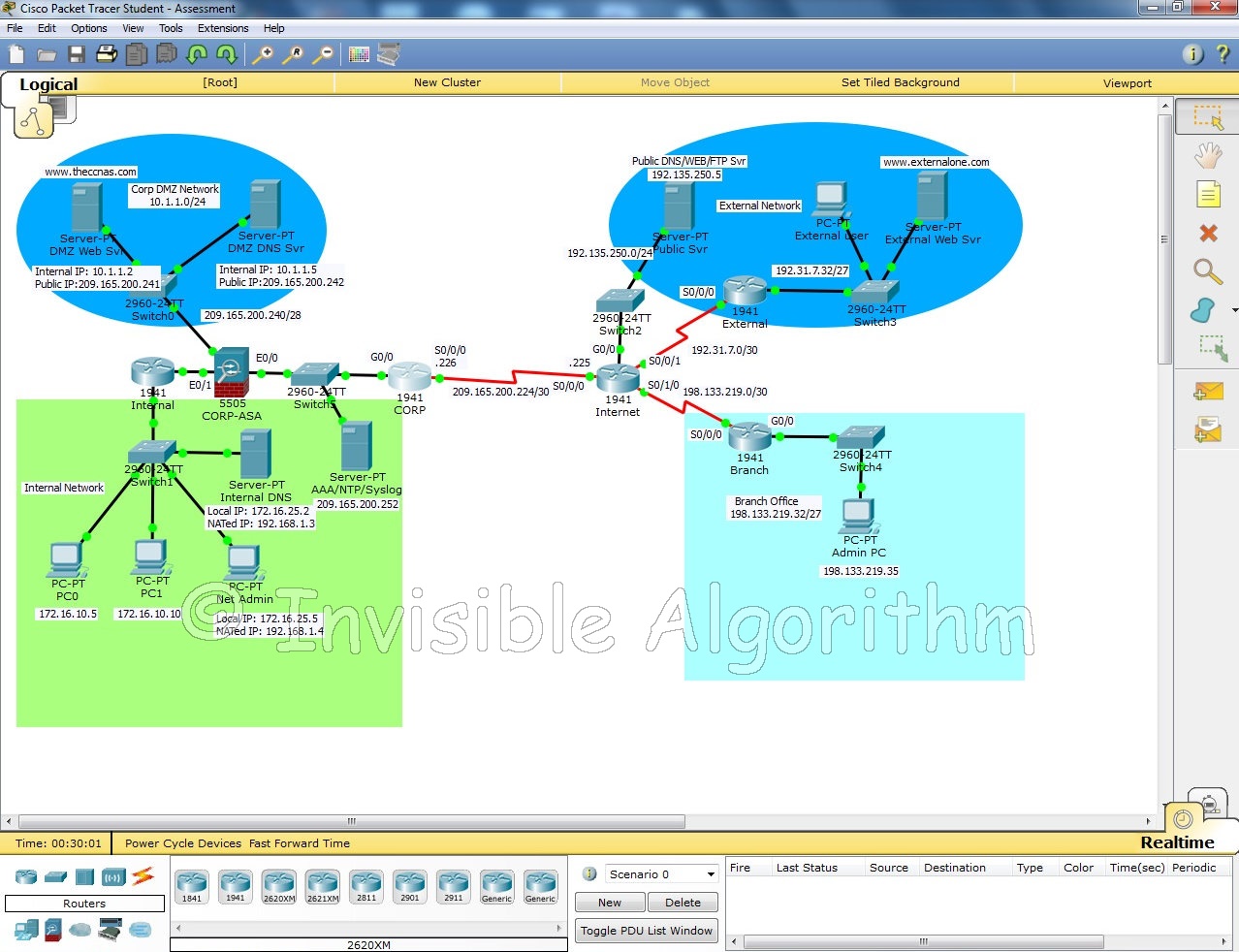
Network security packet tracer. Online Courses 2019-04-21
CCNA Security v2.0 Labs Activities Instructions Answers
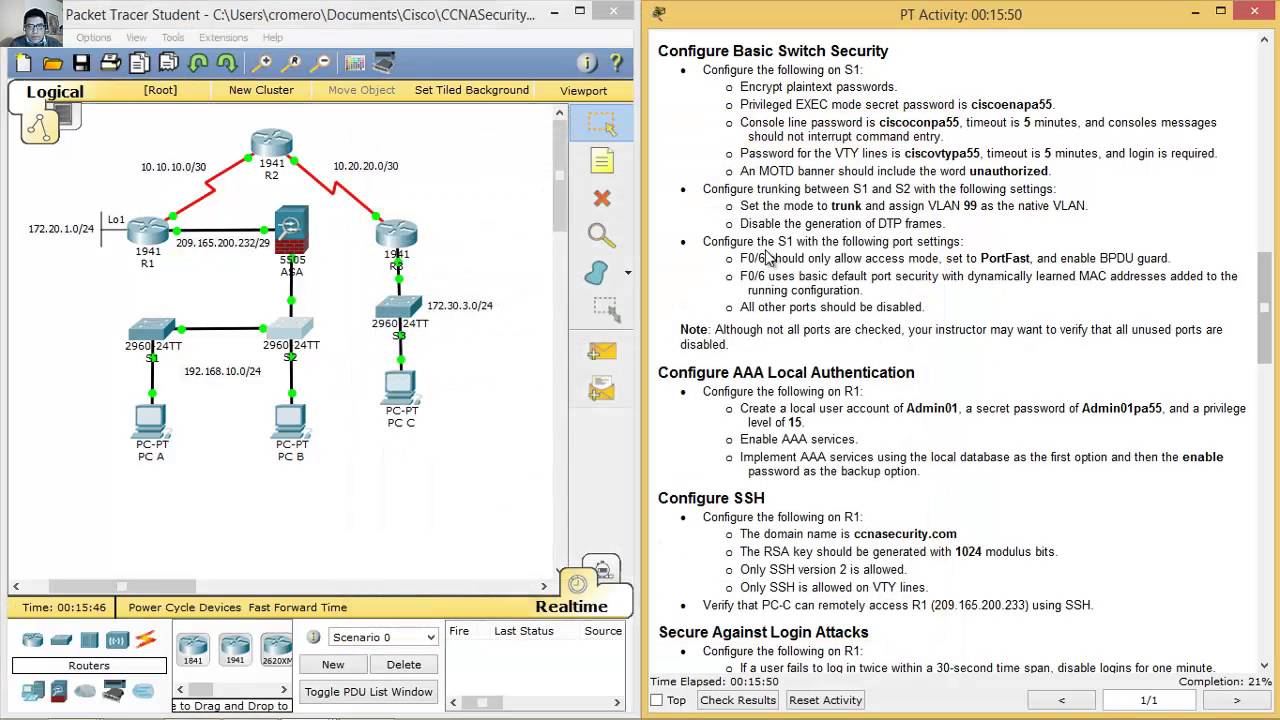
Click lightning bolt button on the bottom left-handed corner and click copper straight—through connection. Step 12 Likewise, if we apply the show port-security command, we can see that there is an increase of 1 in the Violation Count section. As a result if you want to download Packet Tracer you will need to enroll in one of their courses. Port security feature does not work on three types of ports. Note: Log messages can be generated on the server by executing commands on the router. Maximum number of devices that can be associated with the interface is 132.
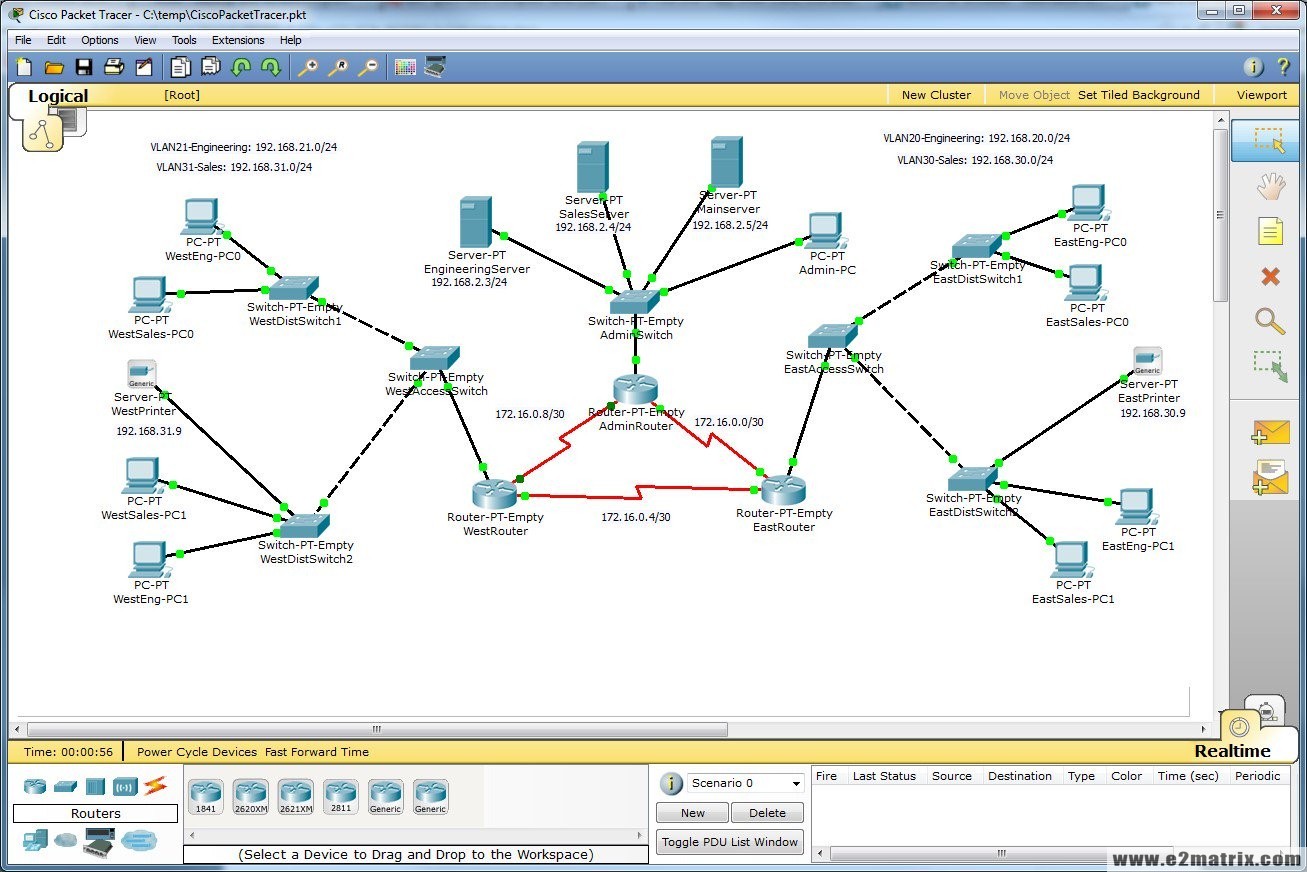
10.4.1.1 Packet Tracer
From Privilege Exec mode use configure terminal command to enter in Global Configuration mode. Answer: R1 config ntp update-calendar Configure for R2 and R3 too Verify that the hardware clock was updated using the command show clock. But after the enhanceents of Cisco Packet Tracer, Packet Tracer commands are also increase and new devices are added. Through integration with other Cisco Security products, Packet Analyzer provides analysts with the ability to capture all the raw packets from network. We recommend you to go thought all version if you are not clear. Step 4 — Configure routers to timestamp log messages.
Ultimate Guide to Packet Tracer
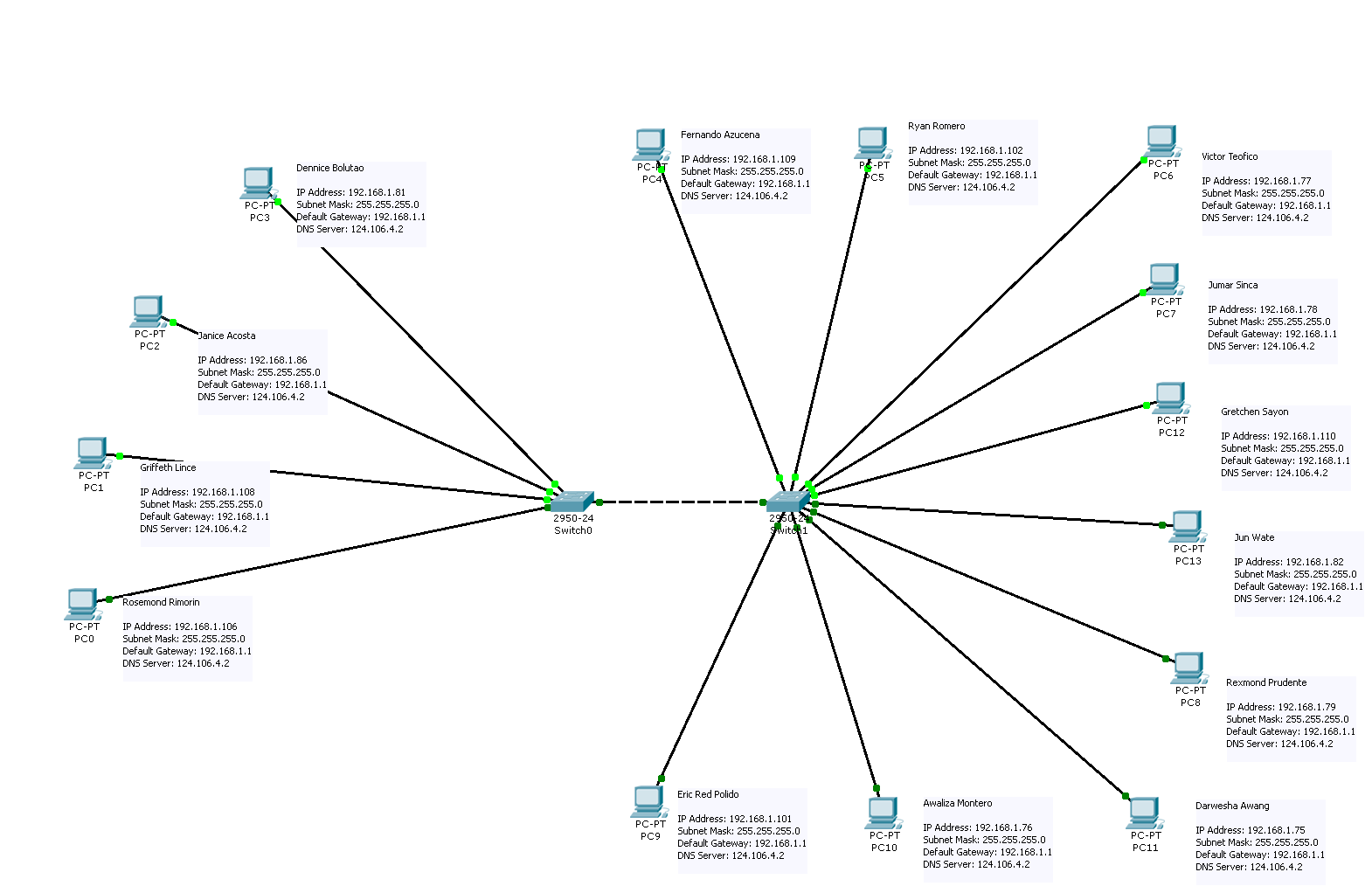
Your completion percentage should be 100%. Answer: R1 config ntp server 192. For a guide on the Packet Tracer labs already on the site, you can check out. Creating topology guides with a tool like packet tracer is preferable to using pen and paper because you can add and remove new features without having to scribbe anything out and start from scratch! We analyze your responses and can determine when you are ready to sit for the test. It depends on your instructor creating your class. How to enable switchport port-security Advertisements Port security is disabled by default.
Online Courses
It is available in different popular global languages. Choosing a key modulus greater than 512 may take a few minutes. Currently they are physically connected by inactive in a state referred to as administrative shut down. If you do not know how to do this, you can check out. However, it is only available to members off the Cisco Networking academy updates can also be accessed via the login portal. In our case, the task specifies that the dmz interface does not need to initiate connections to the inside, therefore our configuration will be as follows: interface Vlan3 no forward interface Vlan1 nameif dmz security-level 50 ip address 172. While this is a limited topology with two computers and enterprise networks are considerably more complex, this will help to teach you some basic principles that you can take with you when managing larger networks.
Cisco Packet Tracer Download For Windows 32 Bit & 64 Bit

In order to configure port security we need to set it as host port. You can create your Network topology by dragging various devices. You can perform by watching the Restrict and Protect operations. Many organizations possess some level of security monitoring and incident response capability. In this mode frames from non-allowed address would be dropped. Skip this command to use default mode.
Switch Port Security Configuration on Cisco Packet Tracer ⋆ www.littleboyblu.com
R3 config ip domain name ccnasecurity. In our scenario we have connectivity between server and pc. You can reach many Cisco commands on the real router with Packet Tracer commands. Features and capabilities Network threats and cybercriminals are getting smarter. Switch config-if switchport port-security violation shutdown Set security violation mode.
CCNA Security Packet Tracer Lab: Introduction to Cisco ASA
But in this mode, switch will make a log entry and generate a security violation alert. The Interface is set to interface access mode with Switchport Mode Access command. There can be some limitations because of the fast that at the end of the day Packet Tracer is a simulator. Use the show ip ssh command to see the current settings. Configure timestamp service for logging on the routers. After successful installation of Cisco packet, you can create topology drag and drop many devices into your topology.
Network Security Packet Tracer Activity Chapter 2 Answer • Invisible Algorithm
Interface will learn mac addresses until it reaches maximum number of allowed hosts. Starting with Packet Tracer version 6. Click Check Results to see feedback and verification of which required components have been completed. Becoming familiar with a tool like Packet Tracer is an important intermediary step in preparing to monitor an enterprise-grade network. Switch learns mac address from incoming frames. R3 config line vty 0 4 R3 config-line privilege level 15 R3 config-line login local R3 config-line transport input ssh Step 4. Interface will learn address until it reach maximum allowed number.