443 ssl proxy list. Free Proxy List — www.littleboyblu.com (ex www.littleboyblu.com) 2019-02-15
HTTPS Proxy List

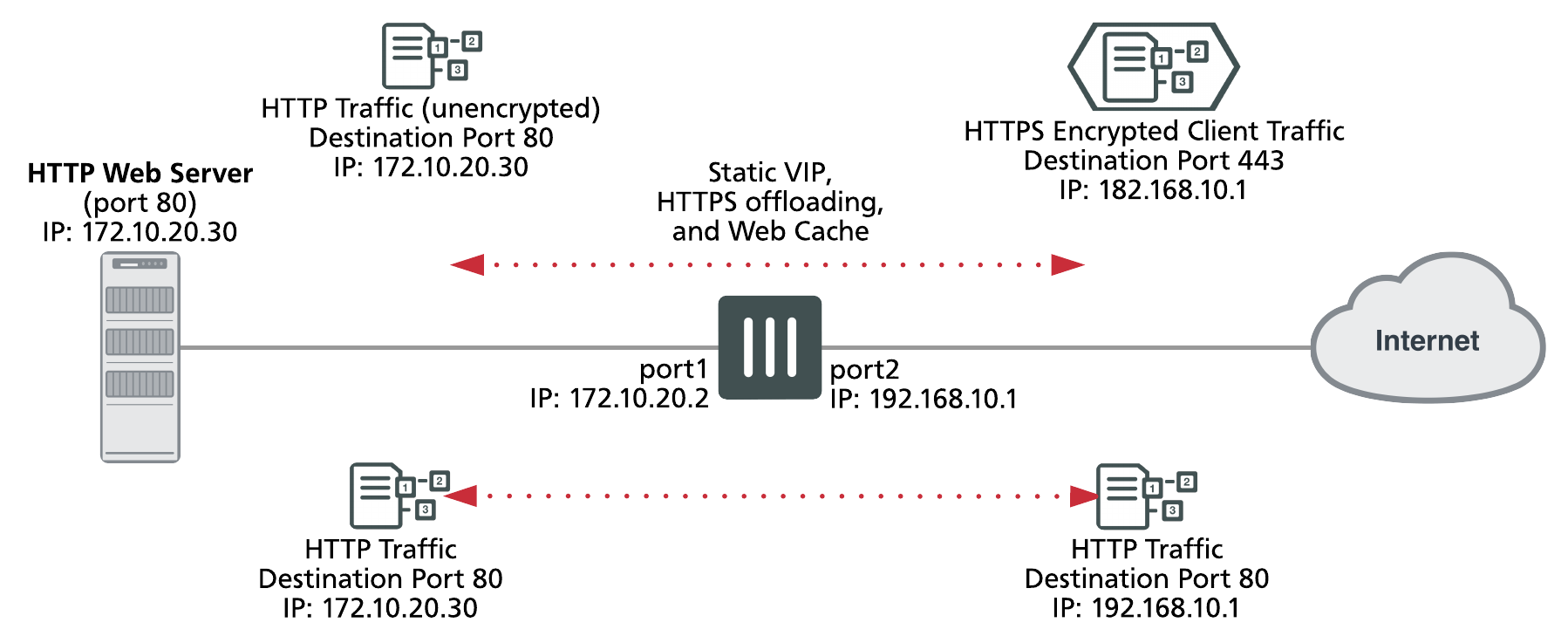
If it's still of interest, here is an answer to a similar question: To answer the second part of the question: If yes, what kind of proxy server allows this? This can be used to identify you, your location, and the websites you visit can be collected to build up a profile about you. We don't need to change this configuration, as it works the same! For more information about how to configure proxy actions, see. It can show you current traffic and if it blocked anything if you configured it to do so :. The job of the load balancer then is simply to proxy a request off to its configured backend servers. For more information, see , and. Our web proxy is browser-based, so you can go online from any device, anywhere in the world. For information about how to export a certificate from a Firebox, see.
HTTPS

You can use the settings on this tab to set logging, notification, automatic blocking, and timeout preferences. You can export the default certificate created by your Firebox for this feature, or import a certificate for the device to use instead. What is a proxy server? Why choose our Premium Free Public Proxy list? To access only proxies that have recently been performance tested, visit:. We use the best-advanced techniques to verify all listed proxies. The Content Inspection Settings dialog box appears. Levels of anonymity These are usually divided into 3 categories. These are somewhat heavy on the network and can be slow as a result.
SSL Free Proxy
You can in one click. After that, the proxy simply decrypts data from one connection, reencrypts and feeds it into the other. Read more on to see the difference between tcplog and httplog. It receives the client-initiated connection, and then initiate another connection to the real server. After it examines the content, the Firebox encrypts the traffic with a certificate and sends it to the intended destination. The Content Inspection tab is selected by default. You can enable or disable the predefined exceptions.
Python: HTTPS using a proxy server with requests

I downloaded their client software, installed it and have the service turned on. If a domain name rule is matched, the action from that rule will always be applied. People often choose this option when their goal is to visit blocked websites, bypass firewalls or download from file hosting sites — rather than hide identity. When you save the configuration to the Firebox, or save the configuration to a file for a specific Fireware version, Policy Manager automatically changes the configuration to be compatible with the lower version of Fireware. However, these proxies cache the website pages you visit. For a proxy policy that allows connections from your internal clients to the internet, use the Client proxy action. For information about how to use certificates with content inspection, see.
Python: HTTPS using a proxy server with requests
You can also upload your own certificate to use for this purpose. Next, after the certificates are created, we need to create a pem file. Application Control Tab If Application Control is enabled on your Firebox, you can set the action this proxy uses for Application Control. A proxy enables you to visit websites anonymously, access blocked websites, and hide your identity. This option is disabled by default. A good vpn will drill through the firewalls and blocks and eventually find 443 out. All other tradenames are the property of their respective owners.
Anonymous / SSL / Https Proxy Server: SSL Proxies

WatchGuard, the WatchGuard logo, and Firebox are trademarks or registered trademarks of WatchGuard Technologies, Inc. However, many do provide a bundle file. The Content Inspection Summary section shows the current Content Inspection configuration settings. The Content Inspection Summary section shows the current content inspection status and configuration settings. This may provide the best of both security and ability to send the client's information.
Using Squid to Proxy SSL Sites

The backend, luckily, doesn't really need to be configured in any particular way. The Content Inspection Summary section shows the current Content Inspection status and configuration settings. However, these proxies cache the website pages you visit. When you go to a website which uses the https at the beginning you are connecting to port 443. The information can be sold to companies to advertise their products to you.
SSL Proxy List

Or, to create a new Geolocation action, click Add. Proxy Action Tab You can choose a predefined proxy action or configure a user-defined proxy action for this proxy. To enable or disable predefined content inspection exceptions, content inspection must be enabled in the Domain Name Rules or WebBlocker settings in the proxy action. For information about proxy actions, see. For more information about Geolocation, see. .
www.littleboyblu.com
This option can cause certificates to be considered invalid if there is a routing error or a problem with your network connection. The information can be sold to companies to advertise their products to you. The way like that to ensure if it works you can set to 0. You can also create a new Traffic Management action. This routes client requests from a web browser to the internet, caching for increased speed while keeping you anonymous.
HTTPS Proxy List
A pem file is essentially just the certificate, the key and optionally certificate authorities concatenated into one file. When you go to a website which uses the https at the beginning you are connecting to port 443. This option is automatically enabled when you enable content inspection. Geolocation Tab If Geolocation is enabled on your Firebox, on the Geolocation tab, you can select the Geolocation action for this proxy. WatchGuard, the WatchGuard logo, and Firebox are trademarks or registered trademarks of WatchGuard Technologies, Inc. Send me notifications when members answer or reply to this question. The Geolocation tab is available in Fireware 12.