Adobe pdf crack password. How to Crack PDF File Password after Forgot PDF Password 2019-03-28
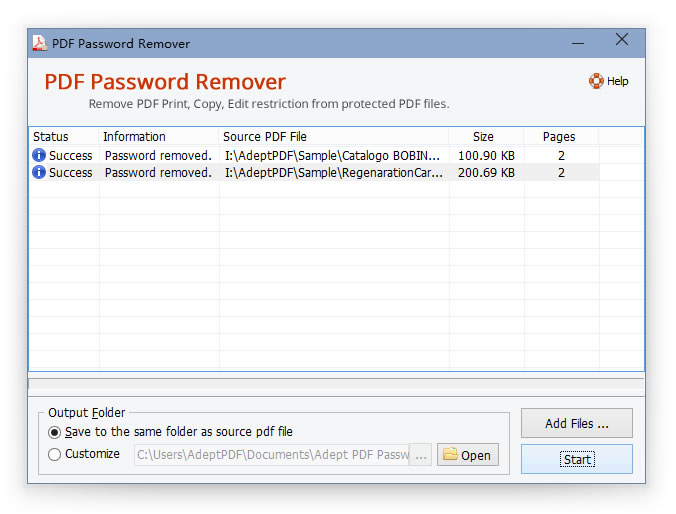
How to Remove or Bypass PDF Permissions Password (Owner Password)
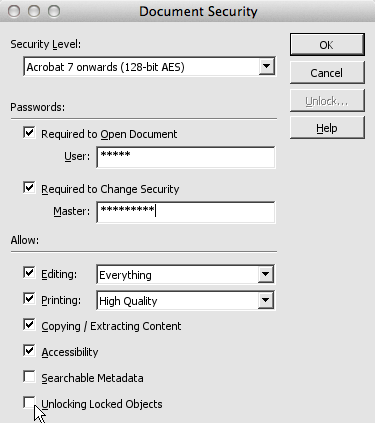
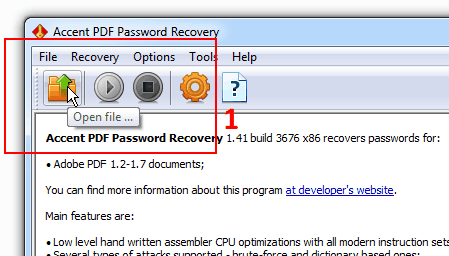
You also need high speed internet connection to process multiple files. So, there are a few efficient methods available, 3 of them are discussed below. You can choose between Brute Force Attack, Mask Attack, Dictionary Attack. Step 3: Scan password recovery type in Type of attack drop-down list, and choose one appropriate. The result might be great, or not so pretty depending on the desktop resolution, page dimensions, and other factors.
3 Proven Methods to Crack Adobe PDF File Password
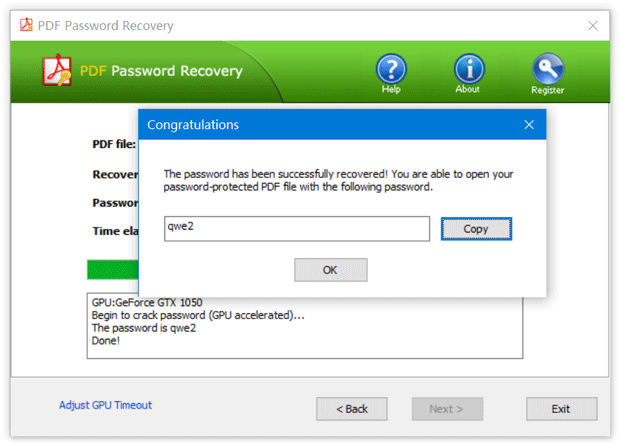
They will try to use all possible character combinations as the password and so the process might take hours or even days and would really depend on your computer's processing power. Once the password is found, you will get a messages with Congratulation word. If you are lucky, the website will process all the files successfully. When if the password is found, the program shows it, as well as the number of passwords which have been tested, and the program speed. Drag and drop the file onto the Chrome Window.
2 Ways to Open Password Protected PDF File without Password
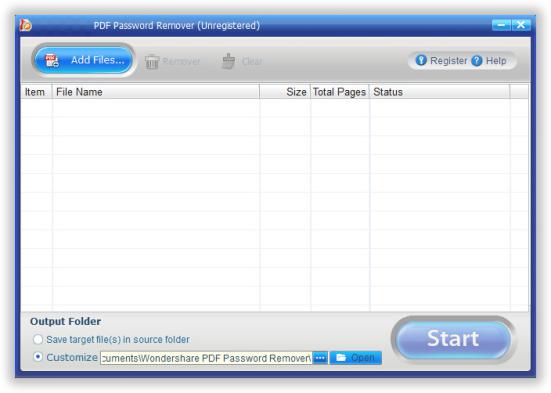
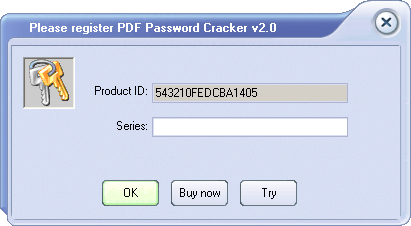
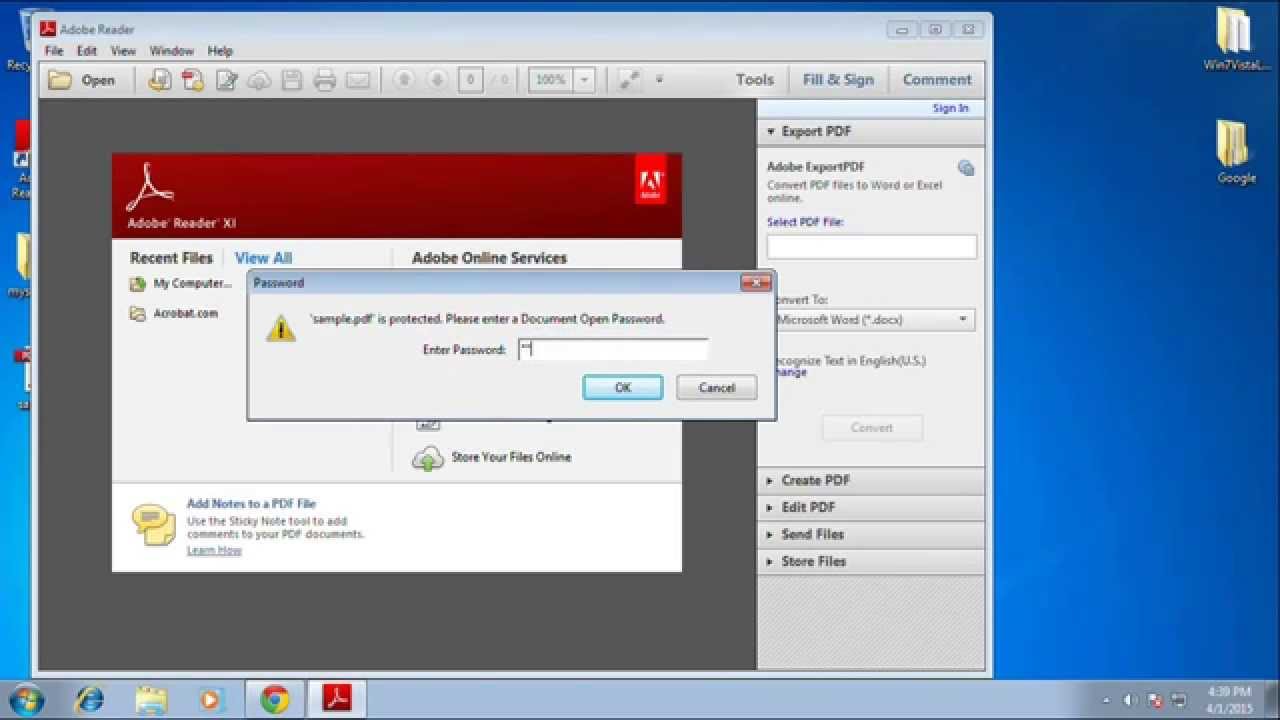
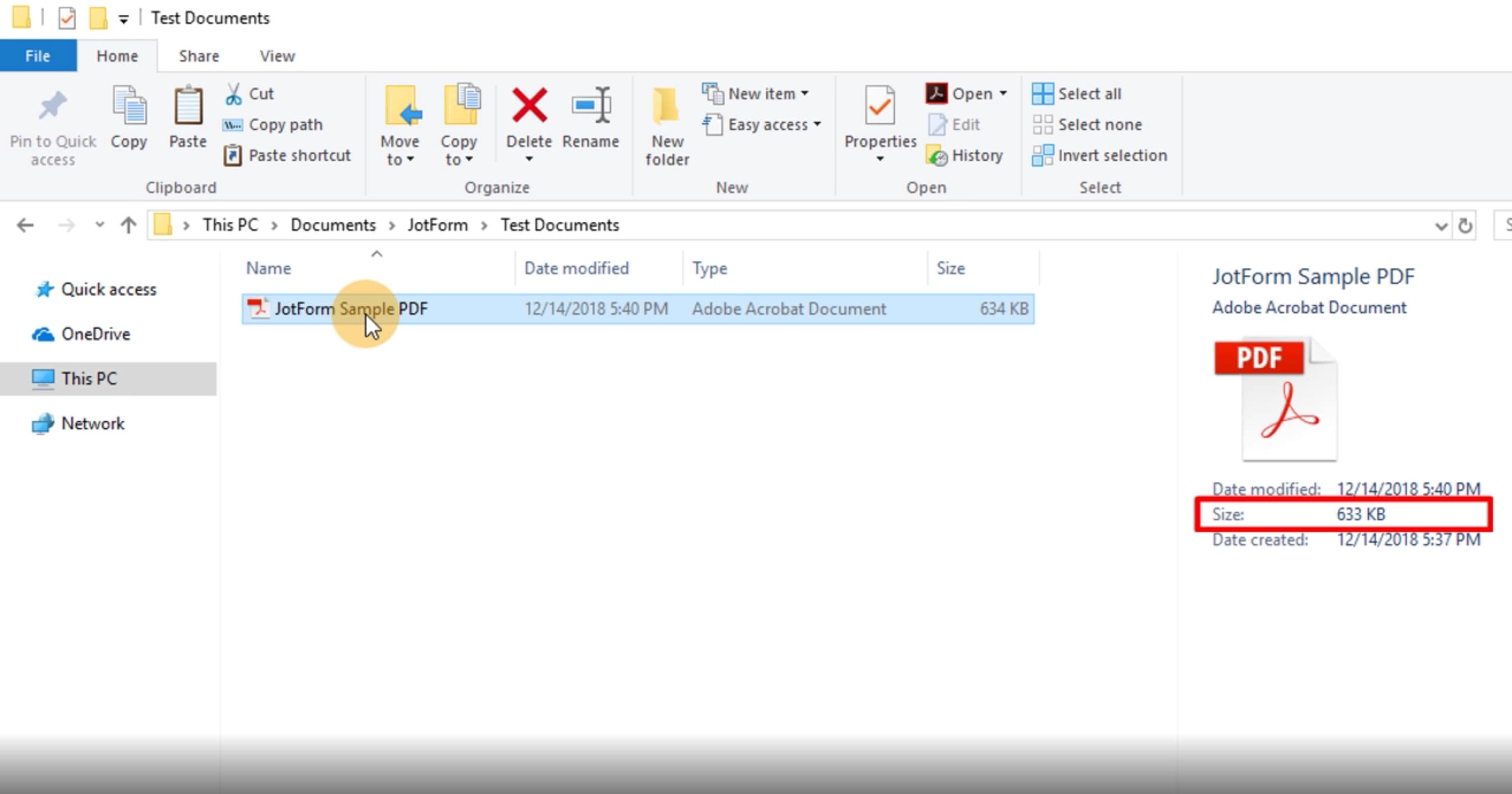
Whether you have found any effective methods? But, there are some serious drawbacks of using the free online tools. Step 1: Download, install and execute on computer. After you download the program on your computer, install and run it, then you will see the main interface like blow. Even though the program still shows consistency in play and never crashed. You can check the security settings by clicking File, then Properties. Once connected and the unlock request finally gets through, the 3rd party server verifies the login and either responds with the actual content, or exchanges a certificate to unlock the file contents for viewing.
How to Break or Crack PDF Password Protected File

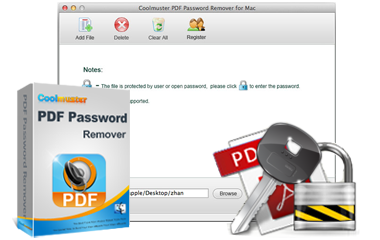
Click the button 'Select Files' or 'Open Files' the button label may vary across sites. Here are the simple steps: 1. Hack Number 2 Tools: , and 's Target: 3rd party , content restrictions. Simply open it up, preferably on a large desktop that can be tilted to where it shows the whole page, and of each page. If you don't remember user password, either, you can get from this link to recover open password and permission password at one time. This hack can not and does not work over the Internet with content locked by a 3rd party plugin.
How to Remove or Bypass PDF Permissions Password (Owner Password)
But do keep in mind; this method might not work all the time! Step 5: When the password is recovered successfully, note it down. You can open the password protected file in Chrome browser and then save it on your hard disk sans the password. Some of these tools also allow you to select multiple files at a time. Here we will use the first option to recover open password. This is the fastest and the most reliable third-party password recovery program you will ever get your hands on for free. Usually a document that uses 3rd party is also restricted using one or more of the following security signatures as well.
PDF Password Crack
Why Cracking is Not Necessary This information is provided for personal, professional, and educational use only! Install it on your computer and then launch it. The attack proceeds offline and nothing is exchaned via the Internet. This presents a problem for students and professionals who travel, or are otherwise not always online. All pages are printed or saved. Password cracking of longer passwords can take days or weeks to crack, so we limit the password length to 9 characters. Furthermore, one could surmise that renaming. We recommend you choosing Mask Attack because it can improve the chance of finding your password.
5 Free PDF Password Remover Software to Crack Any Protected File
The remaining pages appear blank until they are unlocked. You should now be able to see the file within the Chrome Window 5. You're allowed to add up to 200 file a time. We expect to be able to modify our digital assets for our own uses, such as for offline presentation on other devices. Those earlier PostScript drivers have been deprecated, but older versions of still provide them.
5 Free PDF Password Remover Tools
Also, you may have an old file whose password you may have forgotten. They are like books that must be returned to the library. This saves you effort and time. It would have to hack into the 3rd party server to do that! This is just for recover your file password instead of damaging your data. . However, more often than not, you may encounter an error message. So, we are making sure that you are getting the best service possible but recommending the best one.
How to Break or Crack PDF Password Protected File
Illegally distributing Copyrighted material is illegal in most parts of the world. This process may take you a while, please wait for it patiently. Once your finish the parameters then click Start button, then waiting! The document can not be text searched because it is composed out of images, but there are programs that can. Bookshelf apps appear to be proprietary and not recommended. Then you will be asked to select a type of attack, do not be intimidated! Hopefully this will create a series of numbered images there. The moment the lock is removed the file will be available for download. Owner passwords can be found with the -o switch.
2 Ways to Open Password Protected PDF File without Password
But not crack open password, we highly recommend using which is one of the best password break tool you will find. If it can be viewed, it can be screen captured. The new file will be saved on your hard drive and it will be without any password protection. These programs could contain anything. This hole may become patched in later versions. This method entails using to unlock the file via the Internet in the usual way and then print to file.