Computer quarantine ou. Joe's Practice Test Flashcards 2019-01-26
How to Remove Virus placed in Quarantine Chest in McAfee®
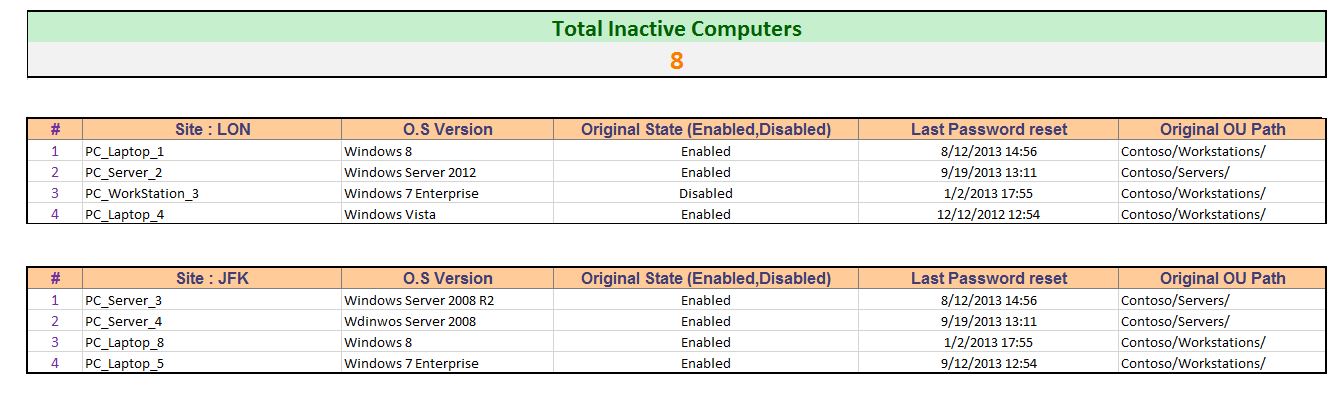
Generating a Stale Computer Records Report using Goverlan Generating a report of computer accounts for which the password age is greater than a specified value is done easily using the Goverlan Scope Action feature. You can also configure any other packet filters peculiar to your organization. For instance, laptops, training or lab computers may not be able to change their password in Active Directory for extended periods. The Policy Configuration Method screen 4. Prompt for consent Prompt for credentials Prompt for consent on the secure desktop Prompt for credentials on the secure desktop A user reports to you that he accidentally deleted a Windows 7 library. You may need to add other valid Internet destinations to add to this list for other IaaS provider, but do not add productivity, entertainment, news, or search sites to this list.
powershell
Some records may still be incorrectly be flagged as stale i. Attacks can include abusing privileges and use of credentials directly from a compromised device, reusing previously stolen credentials prior to enabling Credential Guard and abuse of management tools and weak application configurations on the workstation. Click New and add an input filter for a quarantine resource, such as a Web server, where your profile installer is located. Reset the security level for the Local Intranet zone to High. By requiring an individual to possess a card for logon, you can reduce the risk of stolen credentials being reused remotely.
[SOLVED] By default, AD DS users can join up to 10 computers to the domain...
Microsoft recommends configuring similar restrictions for any 3rd party browsers that you require for administration. Click the Input Filters button, which displays the Inbound Filters dialog box. Quarantine stopped shipping in 1994. This scenario typically requires discovering and protecting sensitive data, services, and applications which may or may not be installed on the desktops. Reset the security level for the Internet zone to High.
Query registry value of all computers in OU : PowerShell

You need to install the latest patches for the operating system. We will test it and see. Do not begin Phase 2 until you have completed all the steps in Phase 1. On the User or Group Access screen, select Group, and then click Add. Note Device Guard must be enabled in order to configure and use Credential Guard.
Query registry value of all computers in OU : PowerShell

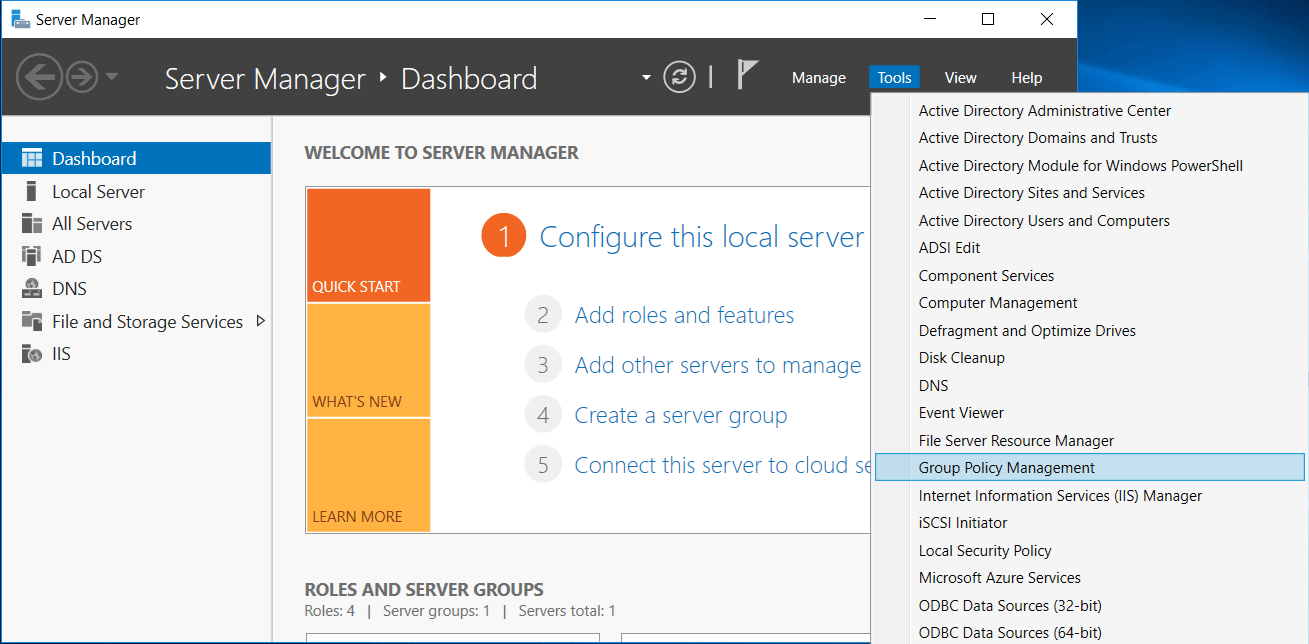
Phase 1 focuses on the administrators who manage your on-premises Active Directory domain, which are critically important roles frequently targeted by attackers. Note Each administrator should use his or her own account for administration. The data must be restored from the Recycle Bin. We can find that information by right-clicking on the domain name, and then Properties in Active Directory Users and Computers. It lists information about drivers running on a computer. Organizations may use only one profile or both.
Detecting and Removing Stale Computer Accounts in Active Directory
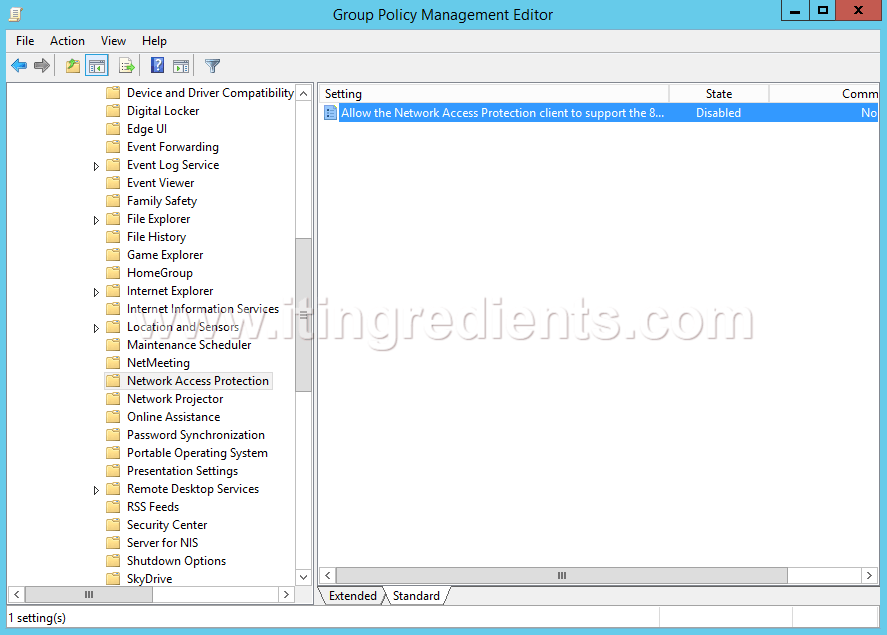
In no event shall Microsoft, its authors, or anyone else involved in the creation, production, or delivery of the scripts be liable for any damages whatsoever including, without limitation, damages for loss of business profits, business interruption, loss of business information, or other pecuniary loss arising out of the use of or inability to use the sample scripts or documentation, even if Microsoft has been advised of the possibility of such damages. Heuristics uses non-specific detection methods to find new or unknown malware which allows the anti-virus to detect and stop if before doing any harm to your system. Now that we have the scope defined, we need to specify the actions to perform on it. The Authentication Methods screen appears. What is the reason for this cursor issue? Select Post-Connect from the Action type drop-down list, and then click the New button to add an action.
Active Directory

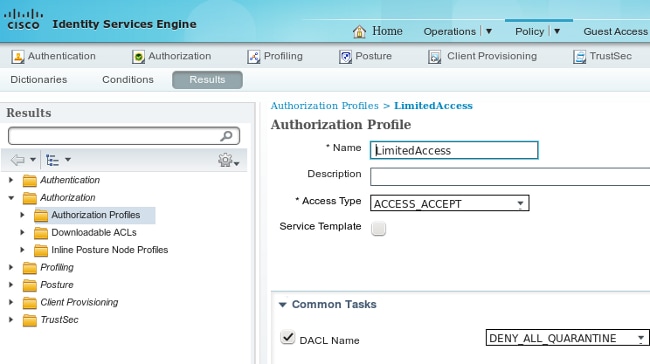
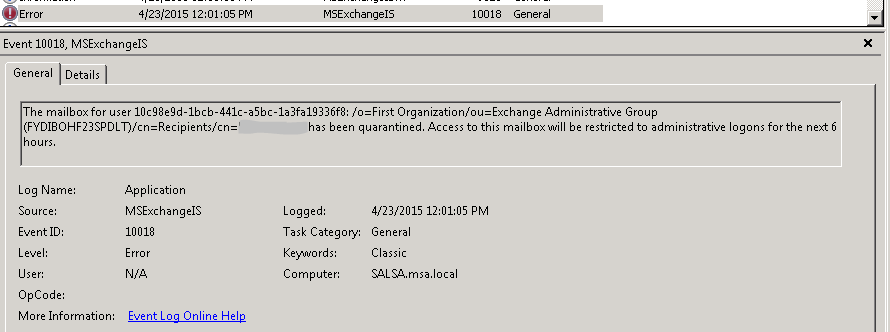
This is a How-To article on using Goverlan to detect and quarantine stale Active Directory computer records. A subscription is Tier 1 if no Tier 0 servers are hosted in Azure. The clean source principle requires all security dependencies to be as trustworthy as the object being secured. A variety of known and unknown attack techniques can be used to gain this level of access. Credential Guard is a new feature of Windows 10 that restricts application access to credentials, preventing credential theft attacks including Pass-the-Hash.
quarantine or remove?
There are two ways you can specify and use a quarantined resource. The first is to identify certain servers on your network because these quarantine resources without regard to their physical or network location. Just delete the quarantined items after confirming they are malware and subsequent scans should no longer detect them. It detects signed and unsigned device drivers on a computer. Run the Action Center utility. I realize this post was a number of years ago, but it's actually more of a problem now than it was before considering the advent of windows 8 tablets and the proliferation of mobile computing. In Program to Run, enter the name of your baseline script.