Conhost exe console window host. www.littleboyblu.com Monero Miner Virus 2019-05-10
Console Window Host (www.littleboyblu.com)

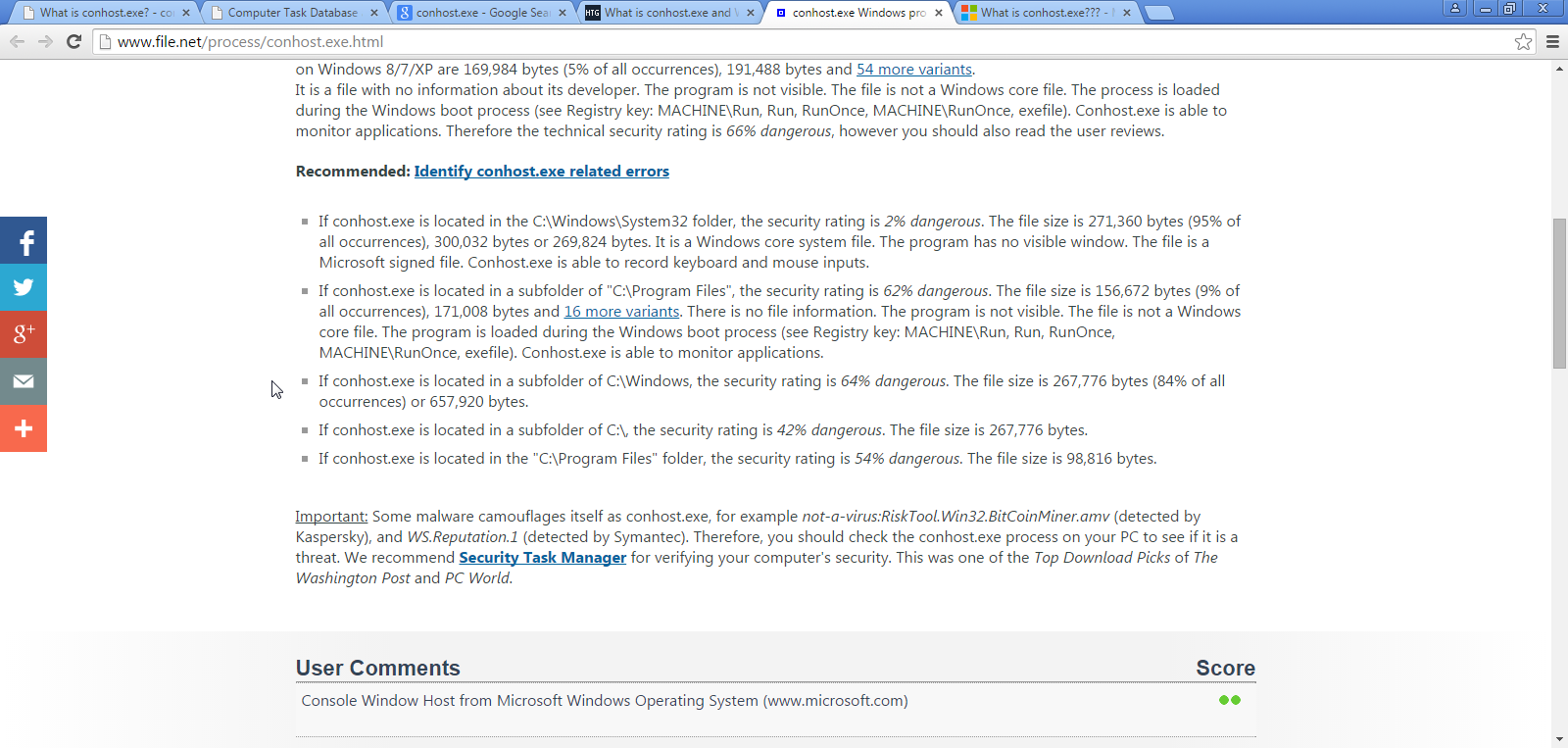
To repair damaged system, you have to purchase the licensed version of malware removal tool. SpyHunter is a powerful malware removal tool designed to help users with in-depth system security analysis, detection and removal of threats such as conhost. To make sure submodules are restored or updated, be sure to run the following prior to building: nuget restore OpenConsole. This can also cause hardware to overheat. I am passionate about computer security and technology. Once you can find it in this folder, it means the conhost. If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove.
How to disable console host (www.littleboyblu.com)

It will diagnose your damaged computer. If HitmanPro does not prompt you to reboot, please just click on the Close button. This will restart your operating system in safe mode with networking. Many Windows users say that their Task Manager is showing a process named conhost. As the time passes, in Windows Vista command prompt get some nice interface look but command prompt still uses the same themes. As a programmer, you must have come across conhost. Hope you find this article helpful.
What is www.littleboyblu.com, why are there multiple instances and how I can fix my high CPU load?
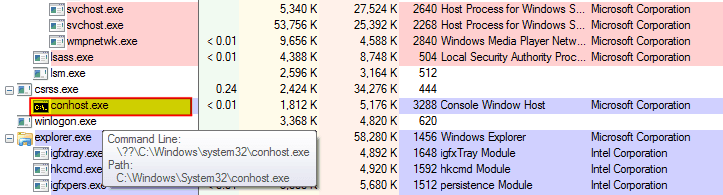
It mentions nothing about how the console appears. I don't have any console windows open. If you check the conhost. How are you trying to login to Phantasy Star Online 2? Step Disable the tasks that you believe may cause issue. After that, navigate to the official Windows Update history site and install the latest Windows 10 build, not older than 15019. Type Command Prompt on the Start Screen. So what you are supposed to do is making attempt to open the File Explorer and see if your conhost can be found there.
How to Delete www.littleboyblu.com Viruses

For the past week I have been analyzing the processes running in Task Manager because I spotted some doubtful activities. In order to make a computer operate normally again and protect the computer's hardware, you should use the guide below to remove this Trojan for free. In this way, it is unavoidable that you are suggested to remove it from Windows Vista or Windows 7 or later. By way of improvement, it is advisable to backup your answers with some sort of source to validate your point. If you are planning to download antivirus software, then download it only from the official site and nowhere else.
How to disable console host (www.littleboyblu.com)
Which browser did you use to login? You can choose any of the three Safe Mode options by pressing its corresponding number and the machine will restart. No until something went wrong on your computer by the conhost. The first intent of the console Windows host is to make the theme of the Command Prompt live in harmony with Windows 7. Since assuming ownership of the Windows command-line in 2014, the team has added several new features to the Console, including window transparency, line-based selection, support for , , a , and more. To remove this malware we recommend using.
Console Window Host (www.littleboyblu.com)

It will not only show you what conhost. Step On the properties popup you will see a path at the top. To remove Console Window Host Miner conhost. Mark Hide all Microsoft services box and select Disable all. Console Windows Host process provides Command Prompt with some exterior features. .
What is www.littleboyblu.com in Windows and Is it Safe?

You might have seen Conhost. Make sure to remember them or write the names down in the case that you want to re-enable them later on 9. Some people are worry that why there are multiple instances of conhost. We've cleanly separated logical entities into modules and classes, introduced some key extensibility points, replaced several old, home-grown collections and containers with safer, more efficient , and made the code simpler and safer by using Microsoft's header library. I can only advice to try to boot the system with barely minimum needed services and see what happens. Generally, cyber criminals trick people into downloading and installing this program to generate revenue.
What is www.littleboyblu.com, why are there multiple instances and how I can fix my high CPU load?
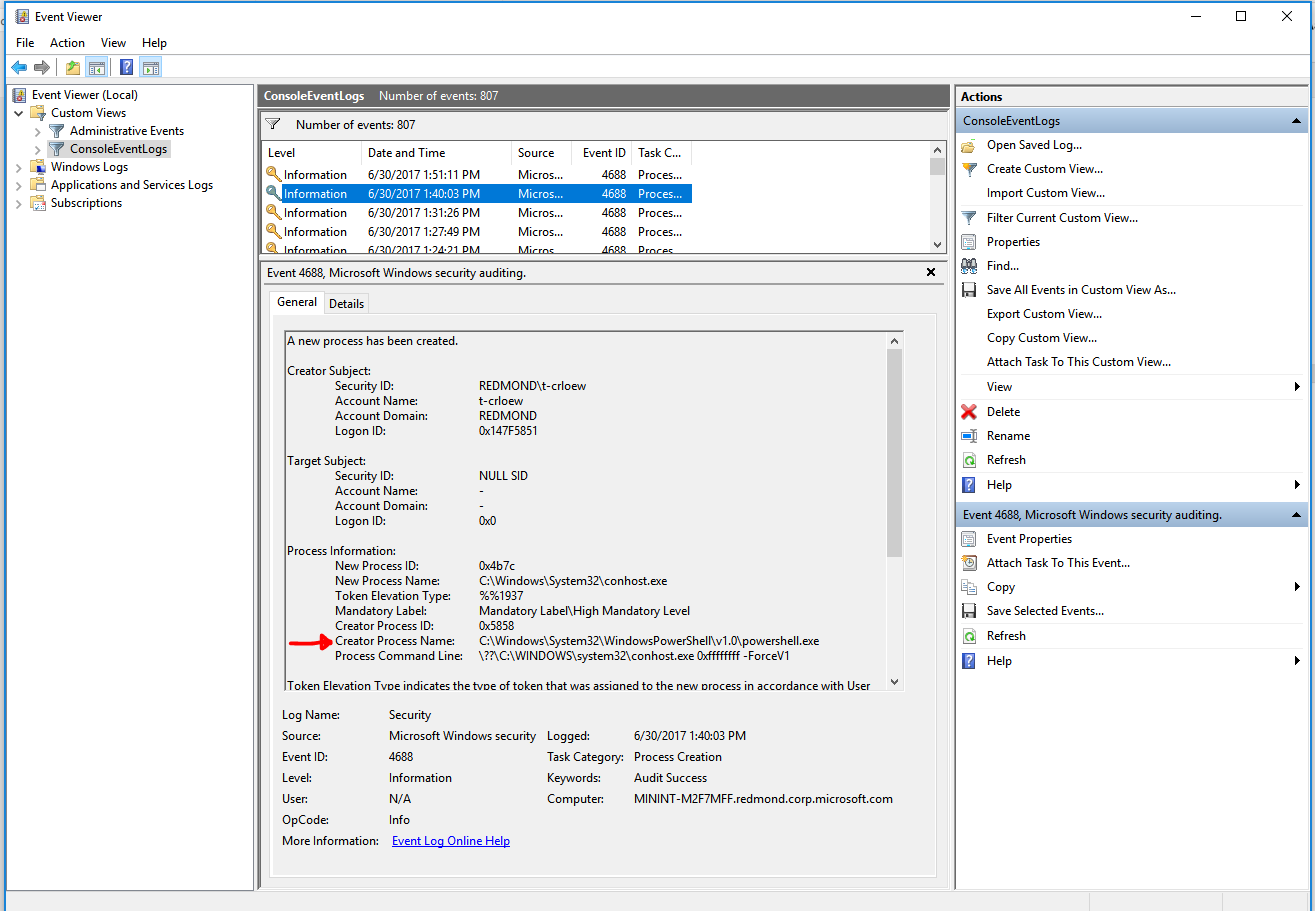
It took me a while to figure out what spawned them, I just got in the habit of killing the processes after booting. Step 5: After the Advanced Options menu appears, click on Startup Settings. This provided something of a bridge for malware to gain unrestricted access to your computer. Building a new terminal When we started building the new terminal application, we explored and evaluated several approaches and technology stacks. It was so because csrss. You will now be shown the settings MalwareBytes will use when scanning your computer. Your computer system may be affected by conhost.
How to Delete www.littleboyblu.com Viruses

If MalwareBytes prompts you to reboot, please do not do so. Right click on the start button and select Task Manager from the list or you can access task manager by pressing Ctrl+Shift+Esc. If you are uncomfortable making changes to your computer or following these steps, do not worry! Can you imagine yourself looking at a Windows 2000-style command prompt in a Windows 7 or 8 or 10 computer? You can also download and install Anti Malware application from Malwarebytes. Start Safari and then click on the gear leaver icon. If the first method does not work, we suggest trying to use decryptors for other ransomware viruses, in case your virus is a variant of them. You may see more instances, you may not. The process itself is an official Windows component.