Crack 128 bit encryption. 128 bit encryption Software 2019-01-11
How secure is AES against brute force attacks?
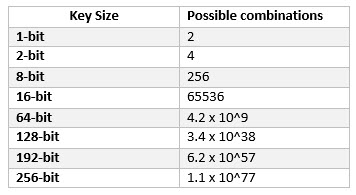
Even if your browser supports 128-bit encryption, it may use 40-bit encryption when talking to other servers or to servers outside the U. As we mentioned earlier, a two-bit key would have four possible combinations and be easily crackable by a two-bit crook. This is a cautionary tale as well, as at any point we could see hardware advance to a point where it becomes trivial to brute force current algorithms. Lock down access to your systems. Password that u enter is not used for encryption, it is used with lot of other info. Again, your security is of paramount importance for us. Whatever breakthrough might crack 128-bit will probably also crack 256-bit.
128 bit encryption Software

I'm currently building a web application and would like to encrypt all data on the back-end. You can probably tell that I don't dabble in cryptology too often. If we really decide to cover all land mass with solar panels to do the job, we can get maybe 4X more power, and get it done in 40 years. I just cracked my two 128-bit wireless networks in roughly 60 seconds from start to finish. They can try repeatedly to decrypt the same recorded message. D in computer science or mathematics.
128

It only allows the specified mac addresses on the wireless network, full stop. So the decided to formally follow the regulations ask for three key sizes but to also do the smart thing the lowest level had to be unbreakable with foreseeable technology. Its a nightmare getting a internet service set up for a foriengner so im looking into hacking a wifi server. Idera software products, such as and , permit you to set the most appropriate for your needs. I'm wondering if it is possible to derive the password from this knowledge in a reasonable time ie.
How To Crack 128 Bit Ssl Encryption
Due to that, attacks against public key, asymmetric cryptosystems are typically much faster than the brute-force style searches for key space that plague private key, symmetric encryption schemes. Does it protect your children on their way to school? Anyway, understanding the difference between symmetric and asymmetric encryption is key to the rest of this discussion. Another annoying thing that most people forget is the following: Key exchange is one thing, but data exchange is another. You are correct - right now breaking most decent ciphers directly is very impractical, to say the least. Everyone knows that it is weak.
How fast can hackers crack 128 bit file encryption?
For those a little more tech savvy and want a little bit of fun buy a firwall such as a pix. As opposed to both parties sharing a private key, there is a key pair. Then again you may also get lucky and find it is the first key you try. What really works for wpa is forced deauthentication and then watching for the handshake as clients connect. On Linux it is just a configuration file to tweak. Your encryption is worth nothing if key is right next to data.
How Safe is AES Encryption?

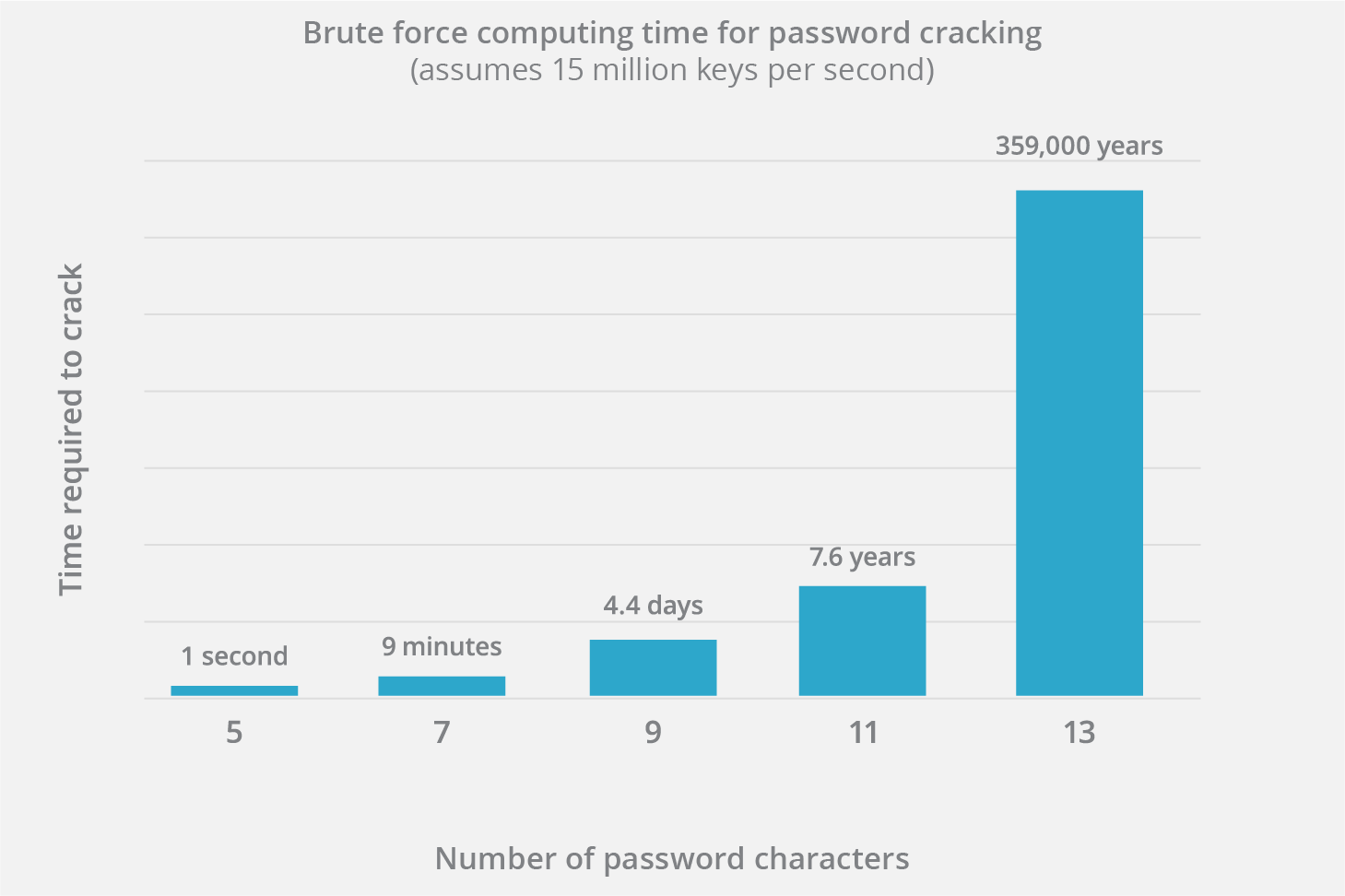
This is more than the age of the universe 13. No Super Computer on the face of this earth can crack that in any reasonable timeframe. Need for Encryption: Below are some situations in which you need a strong encryption. However, that only works if they have a way to assess that they have successfully decrypted it. .
cryptography
It is well tested against state-of-the-art cryptanalysis, and there are no significantly effective attacks against it known. You could also ask about how broken aes is. Brute forcing such a key would not make sense: even if it was technologically feasible which assumes more resources than is available to the biggest governments or corporations currently existing , it would cost a lot more than whatever the key is protecting. I use a 128 bit key size password on our and I am sure no one will break it, for a better security I use a random password generator that maximizes the security of the password. To put that into perspective, the universe is believed to be less than 20 billion years old. Your computer will be at risk getting infected with spyware, adware, viruses, worms, trojan horses, dialers, etc while you are searching and browsing these illegal sites which distribute a so called keygen, key generator, pirate key, serial number, warez full version or crack for 128 bit encryption.
encryption
Did anyone here watch the video? Password that u enter is not used for encryption, it is used with lot of other info. Sometimes key size and security level are intrinsically linked while other times one is just used to approximate the other. The energy argument is a good point. Post navigation Few thousand dollars? Also, because key exchange is the best attack vector for compromising a connection. Would you like to answer one of these instead? The encryption block is 16 bytes.
What is 256

Governments have always had concerns with strong encryption fearing that it could be used against their countries by criminals. Nobody has that kind of time. My sense is that quantum is the biggest threat to data security in the medium term. A-Z and 0-9 means 36 possible characters. That is two, doubled on itself 128 times.