Dlp endpoint console executable. DLP 2019-03-20
Symantec Data Loss Prevention for Endpoint

The agent install was straightforward, but on our endpoint it did not provide any notification to indicate that the install was complete. However, it supports the use of regular expression matching, which allows for more generic matching, if desired. For example, Cisco's Ironport Email Security Appliance turned out to be even more flexible than expected. Documentation provides evidence of remediation for internal audit. With serious data breaches occurring on almost a daily basis, concerns about data protection have skyrocketed.
Data Loss Prevention Endpoint Console does not display in the McAfee Agent menu

It then tailors a long list of available templates. Discover, monitor, and protect sensitive data Business communication happens over an exhausting number of apps, devices and platforms. Surprisingly, we were able to wreak havoc across three products - Websense, Verdasys and Trend Micro - with Google's Chrome browser. Take a breath, download professional software uninstaller here to get some real help now! Wait for the task running icon to disappear before moving to step 2. The central console controls the selection of these features that are available to the end-user.
McAfee DLP Endpoint

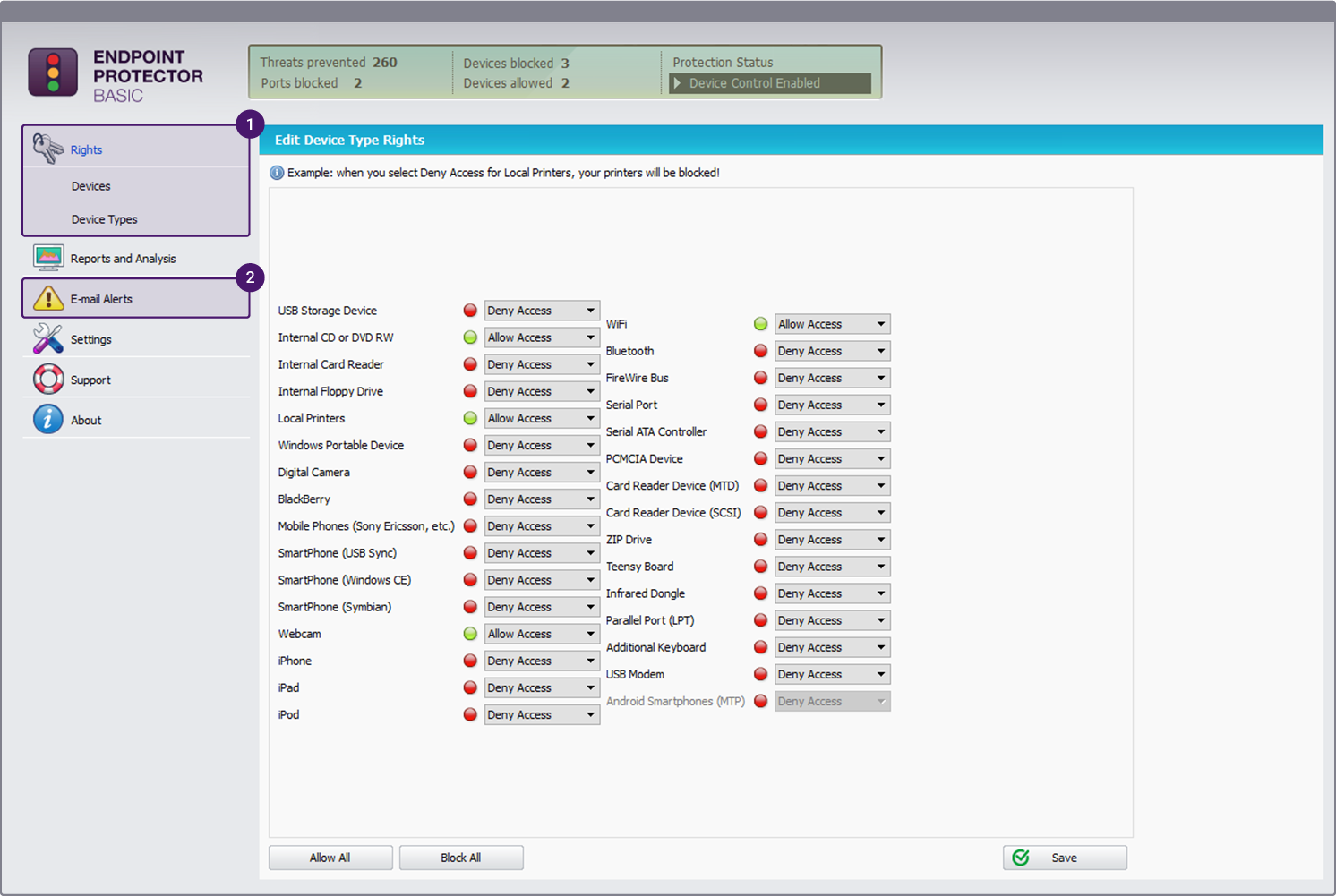
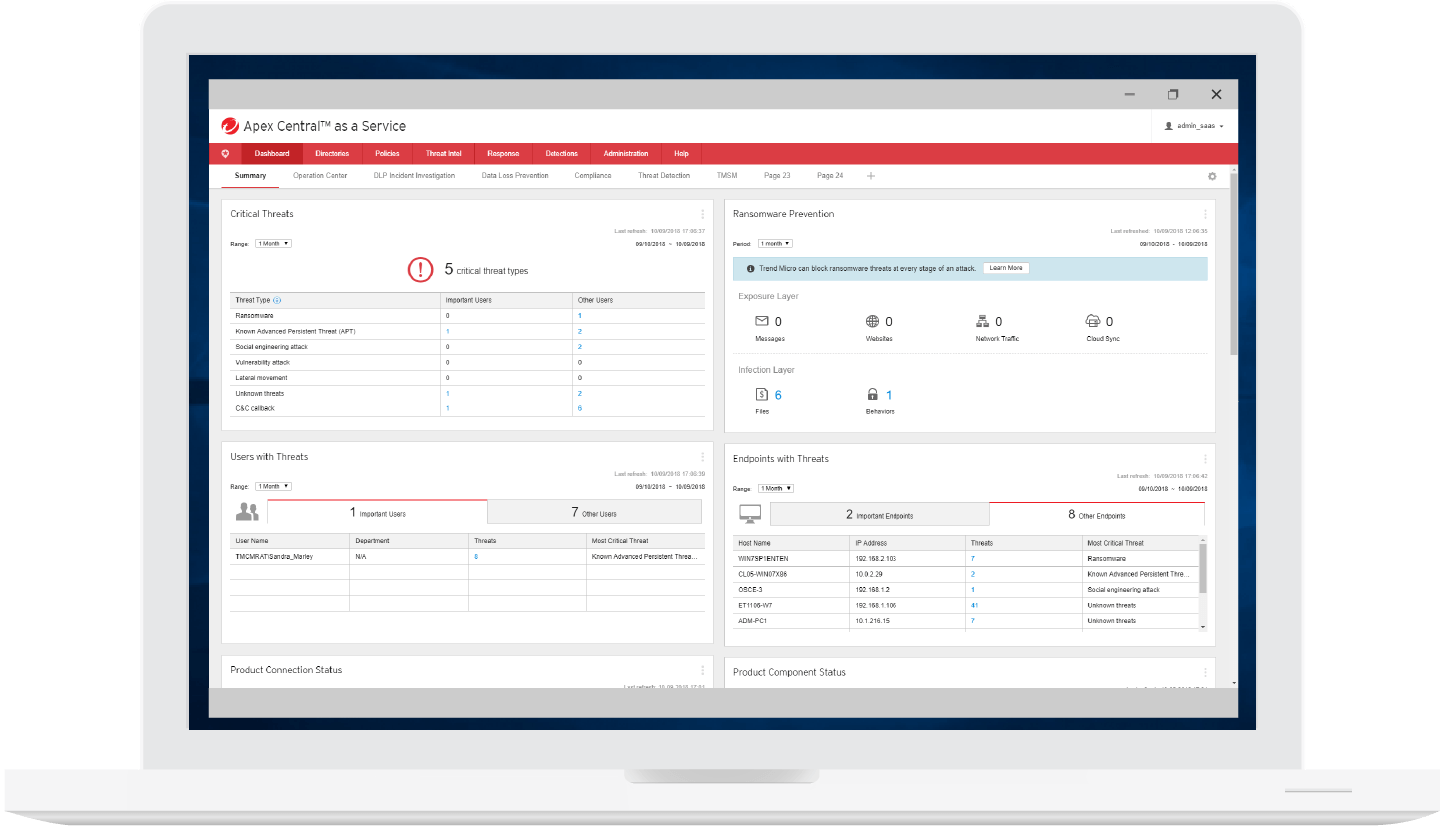
However, this is probably a training issue. As companies look for ways to increase productivity and collaboration, they also increase the number of channels over which employees can leak or steal corporate data. This tool asks the administrator what type of organization is using the product for example, government, finance, healthcare, education and in which locality the product is to be used. The first method is to remotely pull the logs via the Enforce console from the clients. This means that how the data is being used is as important as what data is being used in determining whether to allow the action or not. It gives you complete visibility and control across the broadest range of data loss channels: cloud apps, endpoints, data repositories, and email and web communications.
McAfee DLP Endpoint on the Microsoft Windows platform

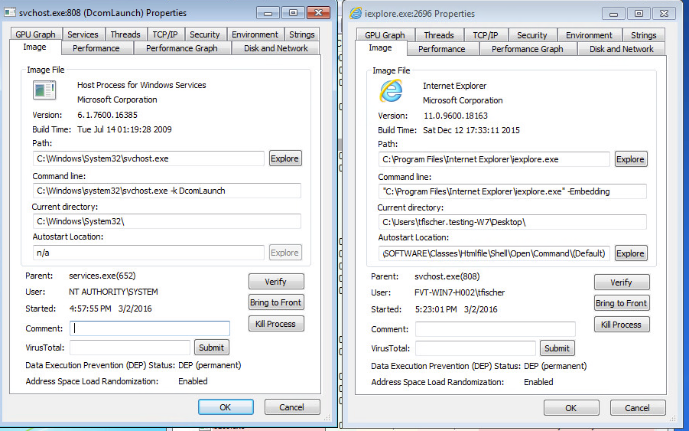
After an orientation from an engineer at Websense, we were able to navigate comfortably around the interfaces. There are two general methods to gathering the agent log files. Classification software verifies that emails and other files are consistently classified and protectively labeled. Since we were in test mode we were more impatient for real-time responsiveness, but maybe in a production environment if it takes a few moments more to synchronize endpoints, it might not be an issue. Data Endpoint and LeakProof can both discover data in this manner, if discovery alone is needed for a system, or if installing the endpoint agent is not feasible or desirable.
Mcafee Data Loss Prevention Endpoint : List of security vulnerabilities
As we expected, policies were enforced regardless of our status as users - i. Only one product, Sophos Enterprise Console, passed all our endpoint tests without workarounds. Endpoint console The endpoint console was designed to share information with the user and to facilitate self-remediation of problems. For example, Larry in accounting might need access to the Social Security numbers of employees, but should he really be e-mailing them to China? So glad that I discovered this valuable tool. Identity Finder's installation process was about average.
Data Loss Prevention Endpoint Console does not display in the McAfee Agent menu
However, the installation documentation was somewhat lacking. Method 2: Local Agent Log File Collection This method is used when the agent is unable to connect to the server and upload the files. While this gives a very fine level of control to the administrator, it leaves one open to a constant stream of new applications that must be detected and added to the policy. Installation None of the installations were particularly difficult, though they all had their minor shortcomings. In some cases, tweaking and workarounds were needed to achieve a successful result. From this information, Data Endpoint builds a customized installer package that can be used to deploy the agent to the clients.
Data Loss Prevention Endpoint Console does not display in the McAfee Agent menu
The vendors told us the workaround was simple enough: block the use of non-Outlook email. Use the first method whenever possible. Since the utility did not start on first login, network configuration had to be performed manually. It was also the most consistent across operating systems and exfiltration methods. For more information, please download the Enforce Platform data sheet. Obviously this will create some issues, as Windows will be cordoned off from them.
McAfee DLP Endpoint

Over 60 templates are provided to enable out-of-the-box discovery of sensitive data mapped to different industry and regulatory directives. An e-mail to support returned an updated Quick Start guide containing a working login though the port diagram was still incorrect. After we reported the problem, Trend Micro provided us with a newer version of their product Version 5. The only limit is the administrator's scripting ability. From this point on, sailing was relatively smooth for LeakProof's installation.
Incidents generated by Endpoint Prevent Chrome HTTPS monitor display the URL as 'Unknown'

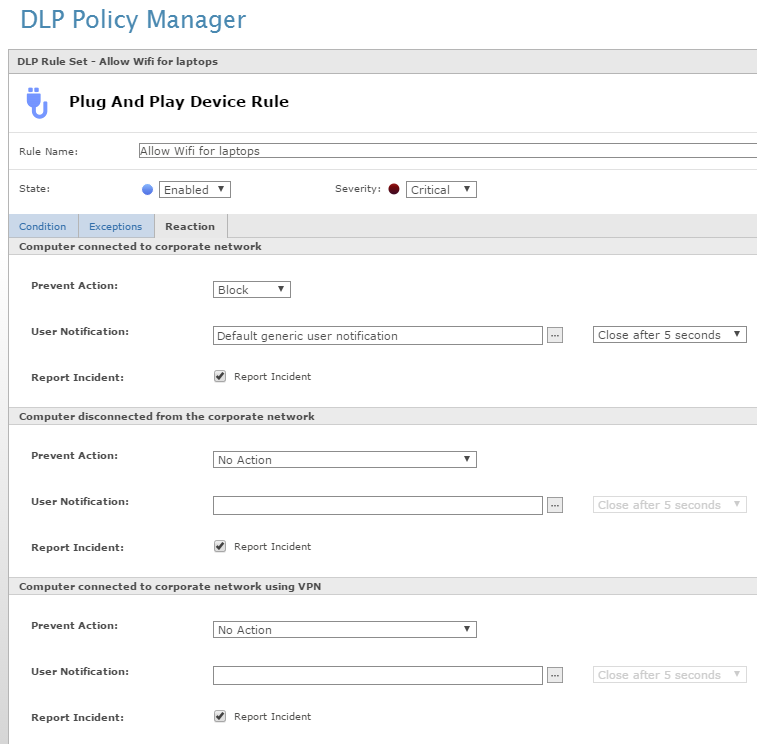
Endpoint Prevent provides broad event coverage over the many ways that data loss can happen on the endpoint and matches that coverage with a broad set of remediation capabilities to properly respond to incidents. All but one of the Chrome test failures were eventually resolved with workarounds. Thankfully, these items were all bundled with the installation files provided, and their installation was wrapped into the installer. But it also has a few rough edges. Data Loss Prevention for Endpoint discovers confidential data wherever it resides and identifies those endpoints with the highest risk.
Steps to collect the Endpoint Agent logs
The Enforce Platform is deployed on a single server and is supported by an Oracle® database, which stores historical incident and system information. Not all Microsoft Visual C++ Redistributable packages appear in the installed programs list on some systems. The management console is accessed via a browser-based interface. The Digital Guardian tagging capabilities allowed us to classify a folder as 'Classified' and thus restrict handling of content in this folder. Endpoint Discover provides three different detection technologies to address different types of data: Describe looks for data matching keywords, expressions or patterns, file type recognition, and other signature-based detection technologies. On the other hand, LeakProof has the capability to gather more information from the user. Product Name: Microsoft Visual C++ 2010 x86 Redistributable - 10.