Email password dump pastebin 2019. Email/Pass Dump 500 [EXCiDiUM] 2019-01-18
What Is A Password Dump?
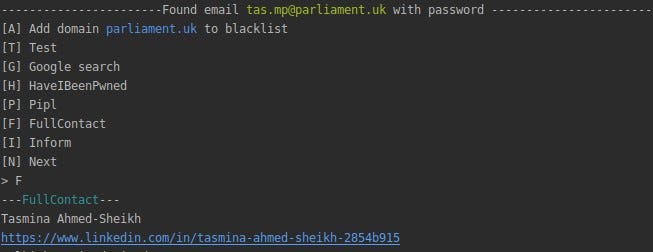
I was passed the cracked list so don't know how it was obtained but looking at the cracked passwords the administrator and developers have a lot of explaining to do. The Threatpost editorial team does not participate in the writing or editing of Sponsored Content. Thanks to Glesec for the tip. Each contribution has a goal of bringing a unique voice to important cybersecurity topics. Moreover, once you have the raw data you need to extract such information and remove all the garbage. The Wall Street Journal Jun 9, 2016 - Instagram has notified millions of users that their accounts are at risk of being. Another example of a free service that monitors Pastebin for stolen data is by Troy Hunt.
Swiss Firm Digs Up 300,000+ Usernames/Passwords on Pastebin

Their iCloud with all their personal photos, their email accounts, facebook and instagram are all vulnerable to being hacked once you have this database. We use these list to check for employees that may be impacted by these breaches or close-knit partners. Everything else will not work! To do some basic analysis on this I wrote and since I originally released it I've made quite a few mods to it to generate extra stats that are useful when doing reports to management. Where is the name from? Thanks again to for his awesome cracking skills. For people looking to build custom wordlists from username lists, it would definitely pay to use a tool which could do these little modifications as this happens on most lists I see. As with the previous Manga Traders dump, looking at the years shows a definite spike, this time around 2000-2010, this would link up with the ages of children of parents are likely to be using the site. Also made cracking a lot easier as the keyspace was massively reduced.
Onliner Spambot dump exposes 711 Million email and passwords
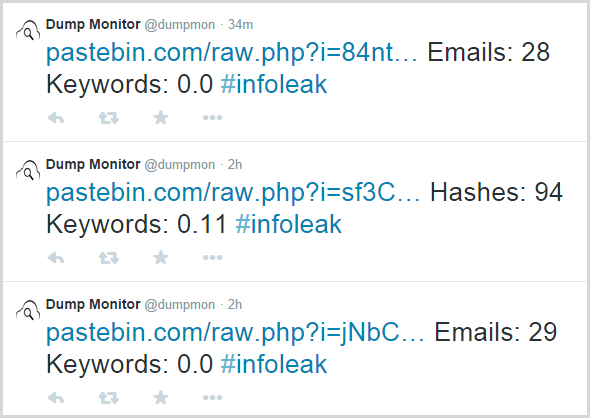
Coming up with a password is hard for some people. Detailed information on the processing of personal data can be found in the. As a result, information such as valuable login credentials can be exposed and compromised when a social platform provider gets hacked. Some of the more popular dumps you can find around everyone has rockyou, 000webhost isn't hard to find, and Adobe is still available via torrent. In an era when new consumer data breaches are disclosed daily, fake claims about data leaks are sadly becoming more common. The pace of these dumps is so high that it's not humanly possible to collect them all, so we have to rely on a bot, scraping PasteBin site for interesting filea.
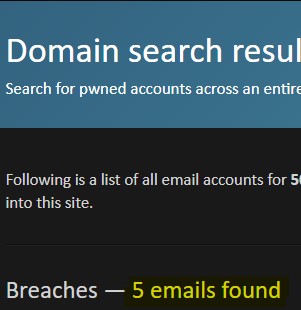
Swiss Firm Digs Up 300,000+ Usernames/Passwords on Pastebin
The administrator of your personal data will be Threatpost, Inc. Guess it's just a waiting game to get my account back. This is why it is stressed in security circles to not use the same password on multiple web sites. Here is a screenshot from the leaked data. If you do not then you can probably be assured that if any hacker tries to take the time and figure it out then they will be able to. Inevitably, some media outlets will post stories questioning whether the company was indeed hacked, and the damage has been done.
Crunchyroll accounts and passwords leaked on pastebin : Crunchyroll
While it may not be your fault that your password has been exposed you are still going to be affected. Thanks to for the tip. The data can be found as a torrent on. Even the old ones are somewhat valued among attackers, and legitimate researchers don't usually go handing out other peoples passwords. There were multiple files, I couldn't find part 1 and I don't think part 6 was the last one but the last one I could find. The way I built it was to try to keep each chunk of stats together as a distinct group so that if I wanted to add a new, similar, group then it was easy to just copy and paste the group.
Email Password Dump : Free Command

If anyone knows how to correctly deal with different encoding types, especially with regards to regular expressions, please let me know. Their bad security was discussed in depth over a year ago by myself and and it doesn't seem to have got better since then. That way cracking the security on one site doesn't expose your entire life. Please remember to read the wiki before continuing: Finally, this is a super-alpha release, so things may be broken or not working as expected. Also haveibeenpwned have created a website where you can search a password and it'll tell you how many times it's shown up in a breach So if you are unable to download the 10gb dump you could try your luck there.
Pipal, Password Analyser
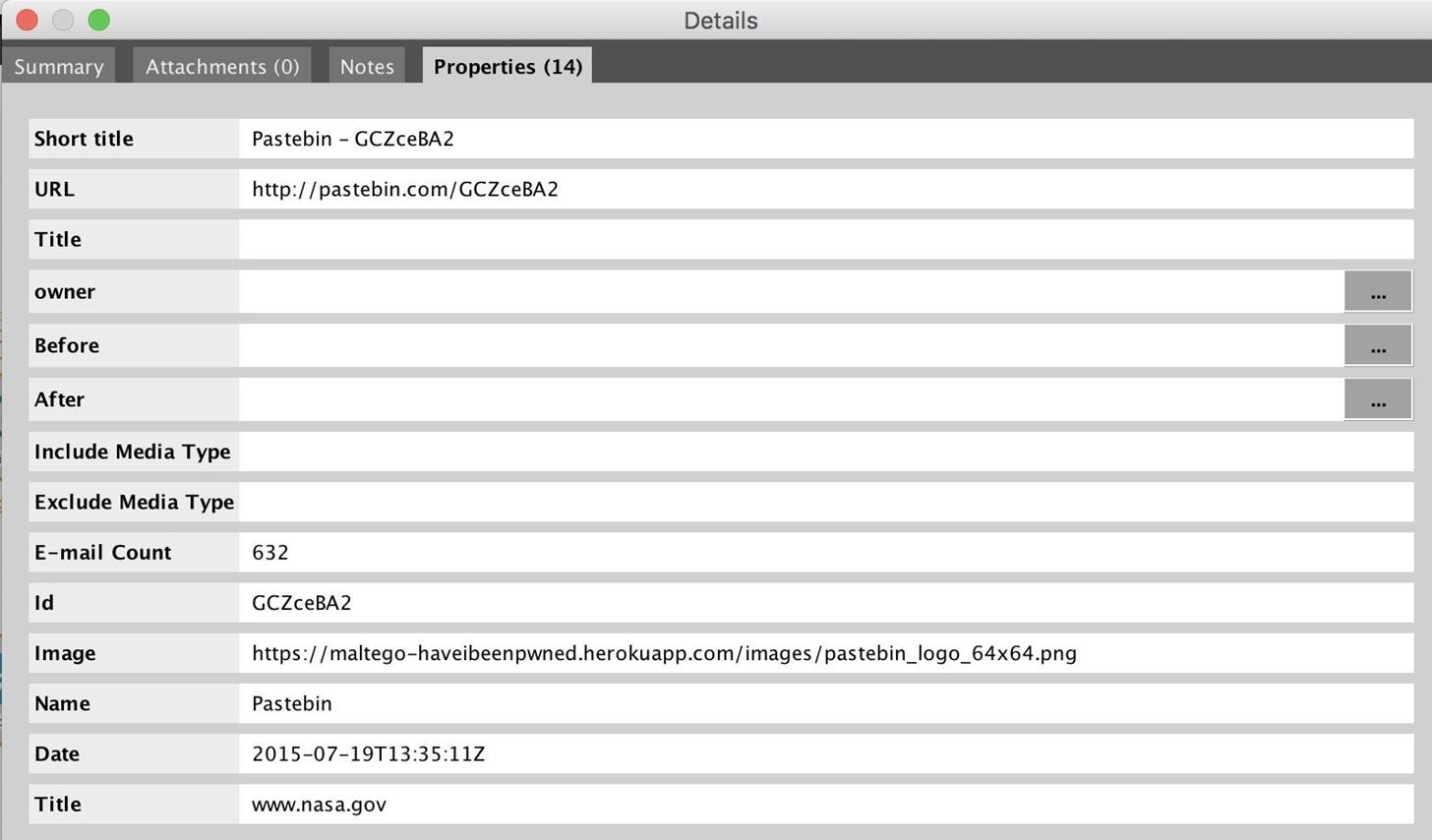
The file is 10gb and you'll need a torrent program like Utorrent to download it. To do so, there are only two options: create it or buy it. That's the reason why Dump Scraper was born: inside this repository you will find several scripts to fetch the latest tweets from Dump Monitor, analyze them discarding useless files and extract the hashes or the passwords. If several of the email addresses in the claimed leak list do not already have accounts associated with them at the allegedly breached Web site, the claim is almost certainly bogus. Usage is fairly simple, -? So where do we go from here? While some of these could be parts of other words, red and dating go together. Jun 9, 2016 - Login Details of 32 Million Instagram Accounts Leaked Online — Time to.
Email/Pass Dump 500 [EXCiDiUM]

Specially for this dump I've created a new checker containing Australian places, this is a quick hack with place names grabbed from a Wikipedia page and I will tidy it up later but it got some matches so shows people pick passwords close to home. This is an analysis of a subset of the passwords that were taken. I define a base word as a word with any non-alpha character stripped from the start and end. It seems that LinkedIn had not been salting passwords when the hack was undertaken and the passwords were only hashed. But sometimes, no matter how secure the password you pick is, there are going to be ways that it can be found. Leaks Archive Database Escrow Marketplace Semi Automated. This is exactly what happens in a password dump.
FULL INSTAGRAM DATABASE LEAKED 2019

Hackers were able to easily reverse engineer the hash and convert the passwords to plaintext. Are people getting into work on Monday after a lonely weekend and using work computers to sign up? The world now knows your username, password, and possibly email address. Running through the LinkedIn lists would have taken many many hours on version 1, version 2 went through 3. Most password managers can generate complicated random passwords or checkout my article entitled Conclusion As security researchers and a corporate security team, we are careful about how we handle the data. The database has been used to send out spams and to users since 2016. Just open up the database in your favorite text editor and Ctrl + F for the email or username you want to hack. These targeted attacks, where malware is delivered to millions of individuals, can spread at higher rates and yield more information.