Fb password word list download. How to Hack Your Friends Facebook Account Password 2019 (Instantly) 2019-04-16
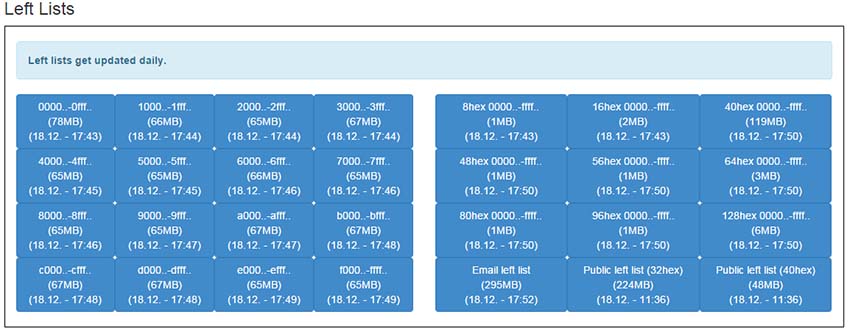
Large Password Lists: Password Cracking Dictionary's Download For Free

He is really capable of doing any sort of hacking you which to like Fb, WhatsAp, Snapchat, wechat,Twitter, and mails, Be careful guys emrys is the man that befits your work. But Toady I'will tell you about hacking in Facebook Using Brute force attack. Fake news is a big problem on social network, they encourage you to make something that you will never have done in real life. Cyberwarzone is the number one cyberwar news provider. I dont even know how many possibilites that is, say for all lower case, uppercase, and 0-9.
Password List Template

When victim login his account by email and password it will save in users. It happens to the best of us especially when you have signed up for many things on the Internet. If you don't know about multi-rules you are in for a treat! The manager can then for each of your accounts, and keep track of it all for you. Also have Elcomsoft Wireless Security Auditor and Proactive Password Recovery , AirPcap Riverbed both installed, but not have the usb wifi device capture Riverbed , so, what is the same of has nothing installed. When you log in you will see something like this this is a cropped screenshot. You can also download it from Torrent. Making a passphrase is simple.
How to Hack Facebook Password in Simple Steps

Download Note: To download the torrents, you will need a torrent client like Transmission for Linux and Mac , or uTorrent for Windows. Moreover it made us want to continue to develop this revolutionary tool. Extracting them in Windows, copying them to a flash drive and than into Beini may be the easiest way. According to them, from a simple picture of your finger, malicious hackers are able to deceive just about any fingerprint reader. There is complete a team working behind it.
CrackStation's Password Cracking Dictionary (Pay what you want!)

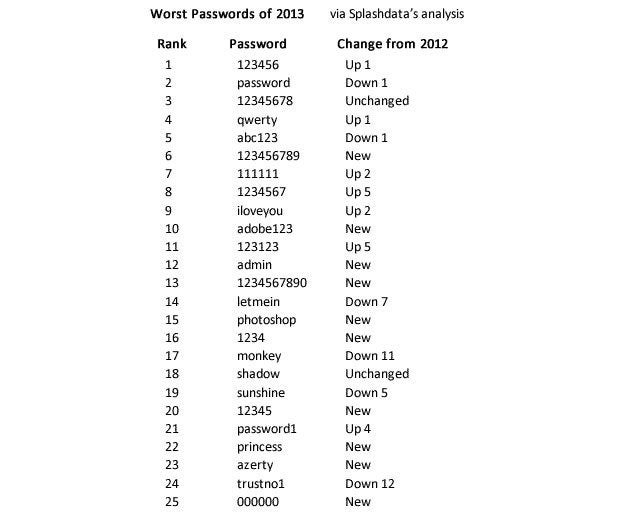
The four-digit password could probably be broken in a day, while the 10-digit password would take a millennium to break given current processing power. It would seem to be ok for jobs that need the site fast but also want it to be safe. What a bootloader is, what it does. You're welcome There are further links as you go through those pages but I thought it best not to post everything. I want to ask them how is going to hack facebook?? Not because it is free. So, keep in mind and go a head to Facebook download online hack tool free from here. It takes forever or so it seems.
WPA / WPA2 Word List Dictionaries Downloads
This increases the turnover of the buyer. How to protect yourself against Facebook hackers? Most security vulnerabilities of residual data occur because of stolen passwords sold on the black market. You can then search the details until you find the login information. I have personally tried it on myself and it really works. Facebook lists These are the lists I generated from.
Openwall wordlists collection for password recovery, password cracking, and password strength checking

After recovery, you can test the password by logging into your account using it. Besides hacking accounts and personal data, creating fake news and their orchestrated circulation, Russian spies also try to coax the American soldiers on Facebook by adding them as a friend. This wordlist is provided as a single text file. This is exactly what hackers want to access to. Anyway, this umpteenth experiment shows that fingerprint readers are not so secure. If you read it correctly you will be able to hack Gmail; twitter accounts too. The key is that the word choices must be totally random.
CrackStation's Password Cracking Dictionary (Pay what you want!)
So Why not learn android programming and create a fake app login. After the launch of smartphones, many hackers had succeeded in tricking the fingerprint reader with a false imprint of latex. The boss is in charge of this criminal organization and gets the money. There are and several in other languages too. Phishing requires specialized knowledge and high level skills to implement. It should sink in after a few uses.
Large Password Lists: Password Cracking Dictionary's Download For Free

In fact, keyloggers are pretty generic and are designed to log the keystrokes. Used by millions of people, it has constant email and chats support facility for any help. How to protect your accountThere is only one way to protect your account by putting the secure password. I think that the formula has to do with the factoral if I remember correctly, as how combinations of 6 charaters are there would be 6! But I have tried these tricks are not working now. It wouldnt have to be up to 16 chars in length, I would settle for like 10. Therefore, I have downloaded oclhashcat-1. Those who purchase databases can use usernames and passwords to spoof the accounts of the service in question, as well as all other accounts.
Wordlists and common passwords for password recovery
Within the email, there would be a link which when the user visits, they would be asked to enter their login information to secure their account. When they dont work crunch works best for me for my dictionary I downloaded every one I could find. It might not even be a feasible option after getting so far up in character length, like 10 characters, I dont know. After verifying you can see the active status and choose to go to Cpanel as shown in the screenshot. Hope may hear from you soon. No need to infiltrate a corps or an administration.
5 Free Password List Templates

If you don't know about multi-rules you are in for a treat! The format of the list is a standard text file sorted in non-case-sensitive alphabetical order. Most security experts believe a password of 10 characters is the minimum that should be used if security is a real concern. Please be sure to check out the for redistribution terms. Facebook hackers use some sophisticated techniques to like phishing, keyloggers. It is very useful to consider this experience as a test.