Google kms permissions. About the google_kms_key_rings Resource 2019-02-27

If you no longer need it, go ahead and delete the Cloud Storage bucket you created in the beginning of the lab. It can be used as a distributed service or in a single geographical cloud data center. Custom Roles also provides the ability to create. The predefined roles allow for a , where it is needed. I appreciate if someone else could give me a hand, and clarify the question. There is a 24-hour delay on encryption key destruction and users have the option to restore previous key versions.
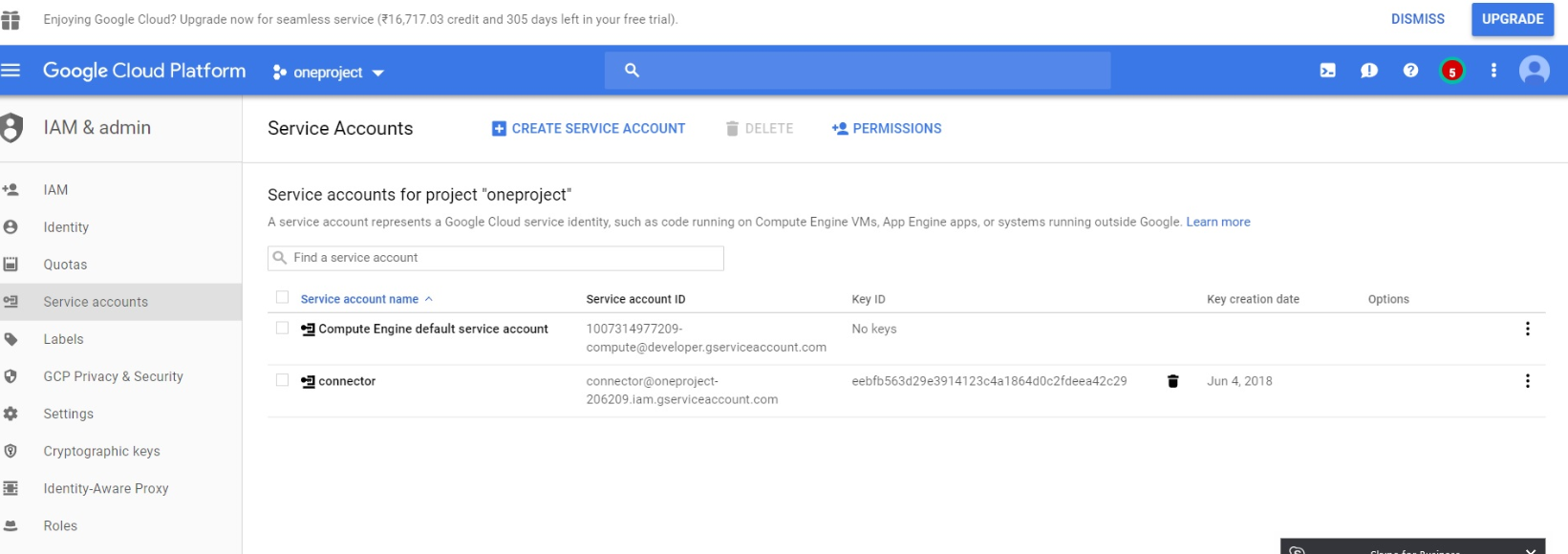
Google: google_service_account
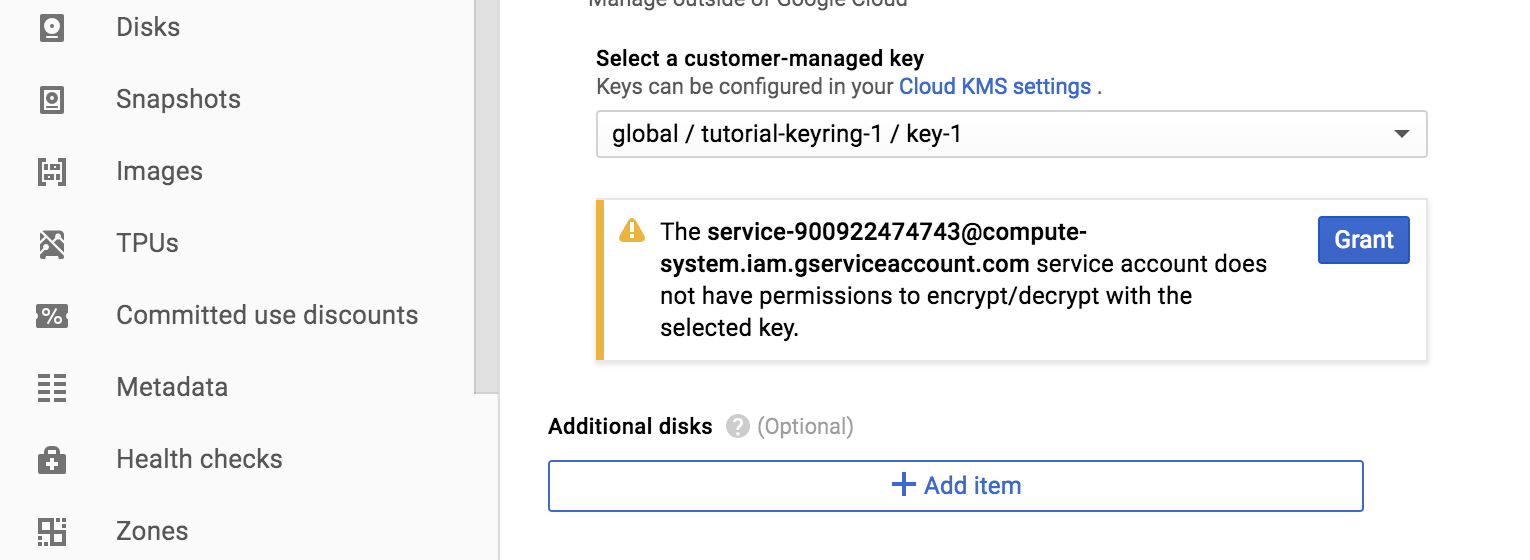
For information about creating custom roles, see. Keep as many active key versions as you want. Or, since the new service account doesn't have Decrypt permission, the gustil cp to restore the file shouldn't work?. Except as otherwise noted, the content of this page is licensed under the , and code samples are licensed under the. Run the following command in your shell: gcloud services enable cloudkms. Without the permissions provided by the cloudkms.
About the google_kms_key_rings Resource
It comes pre-installed on CloudShell and you will surely enjoy its support for tab-completion. It also allows users to restore previous key versions. After your bucket has been created, you are ready to go. Required Permissions The following table lists the permissions that the caller must have to call each method: Method Required Permission s None. For more information, see the Cloud Storage bucket.
Google: google_service_account
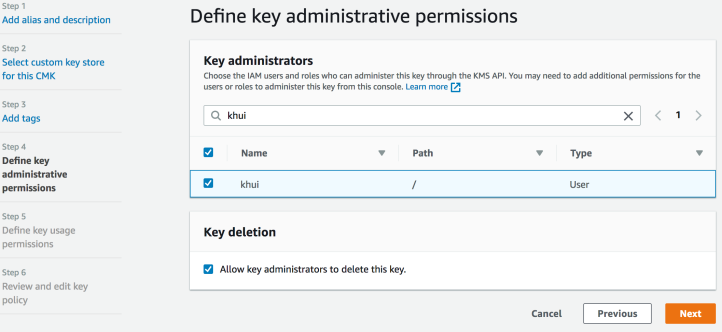
Note that every permission is applicable to a particular resource type. The above command works for images, videos, or any other kind of binary data. However, I have a question related to the permission to restore that file from the same bucket, using a different service account. Get to know some of vCenter's lesser-known features to make this tool. Cryptography is a method of protecting information and communications through the use of codes so that only those for whom the. If you are signing certificates, you probably know the public key of the signing key you wish to use; record the version for the associated private key alongside and you can sign without list privileges.
What is Google Cloud Key Management Service (KMS)?

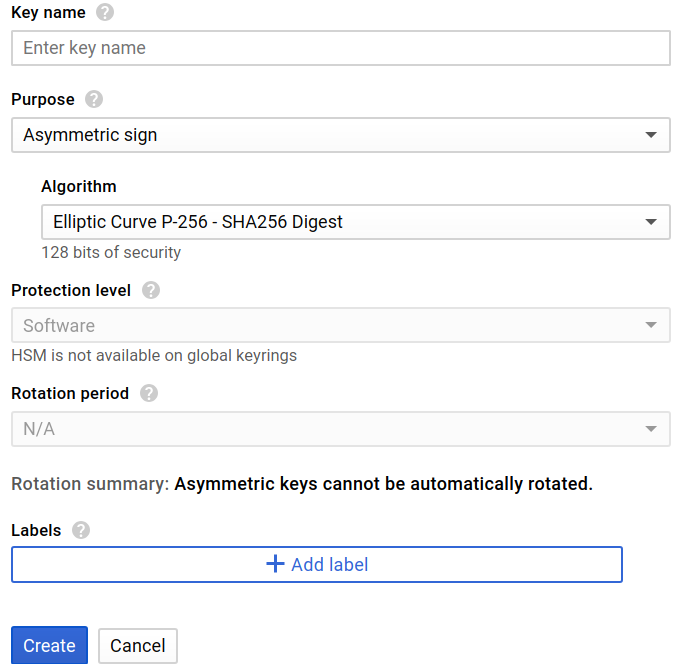
Take the contents of the email we previously looked at and base64 encode it. Retrieve the public portion of an asymmetric CryptoKey cloudkms. You can instead provide your own keys. Scalable, automated, fast Keep millions of cryptographic keys, allowing you to determine the level of granularity at which to encrypt your data. That is, a user who has the role of owner on a Project is also an owner on all the key rings and encryption keys in that project. This list is not considered exhaustive.
About the google_kms_key_ring_iam_bindings Resource
I think it shouldn't work because the service account doesn't have Decrypt permission , or should it work? In order to store the data in this codelab, you'll need your own Cloud Storage bucket. If you're interested, use the same mechanism to check out what is in those other files. Google's offering of an encryption key management service was introduced after Amazon Web Services and Microsoft Azure released their own versions. When you use gsutil cp, you are already using the encryption method behind the curtains. This should display the contents of the plaintext mail file. The encrypted data has information on which key version was used to encrypt it, so the specific version is never supplied to the decrypt endpoint. The main industries Google targets with this service are those subject to regulations about how they store and secure sensitive data, like financial services and healthcare providers.
Use Google KMS to control encryption keys in the cloud

Full documentation is available from. See for more information about the predefined roles. They might also want to encrypt data already in Google Cloud Storage independently of Google's internal encryption. If I have any other in the near future, I'll open a new issue. I give each application sign permission projects. If you don't want the second service account to be able to access the file, remove its read access.
About the google_kms_key_ring_iam_binding Resource

Self-paced environment setup If you don't already have a Google Account Gmail or Google Apps , you must. The question is why I need to give this permission to sign a certificate and whether there is way to sign without getting list of versions. Next comes KeyRings, within which groups of CryptoKeys can be hosted. From your response, I think I need to read a little more about Cloud Storage service accounts things. The response from the previous call can be piped into jq, which can parse out the ciphertext property to the file 1.
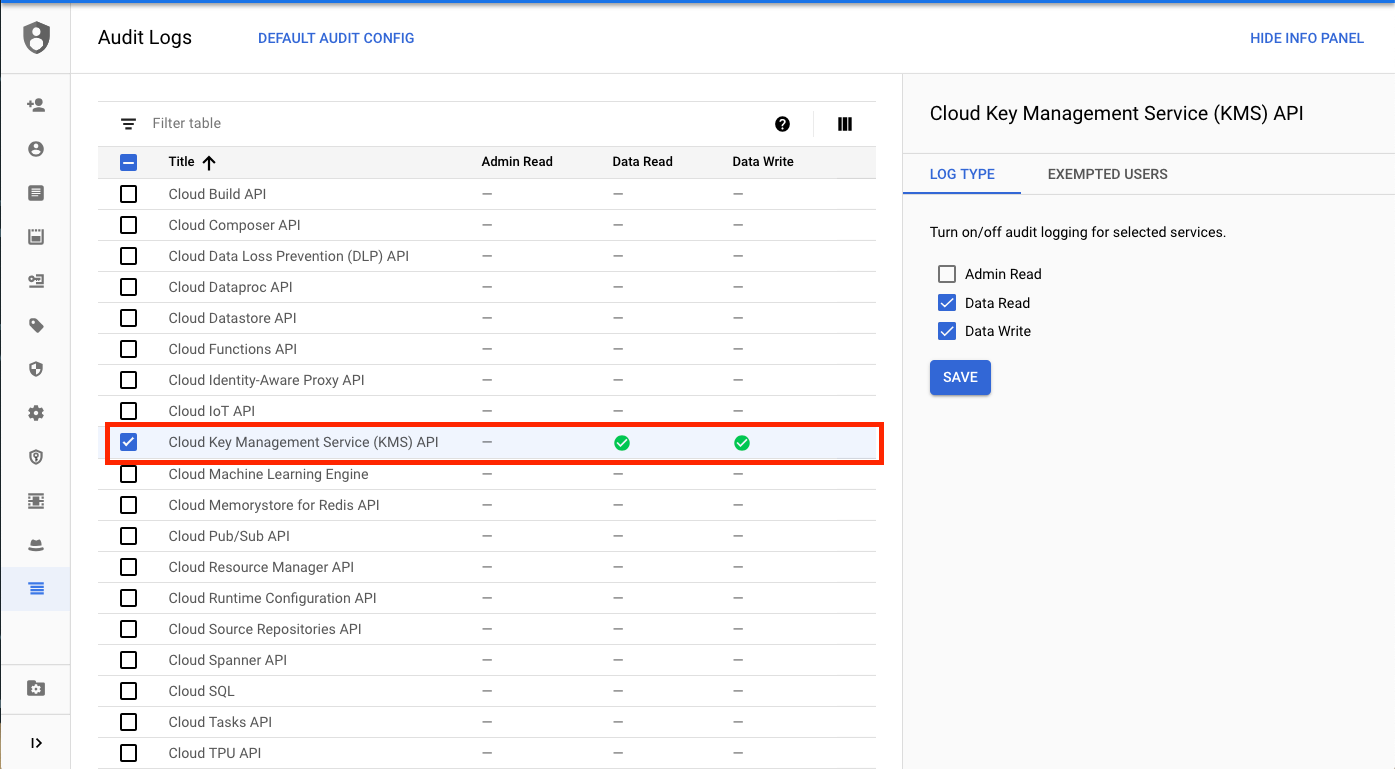
Permissions
Automated and manual key rotation options enable users to apply a preset schedule or manually select when the encryption keys rotate. For a walkthrough on how to encrypt and decrypt data in multiple programming languages, read the. For this codelab, our key ring will be called test and our encryption key will be called codelab. Monitor logs to ensure proper use of your keys. Keys can be grouped by environment like test, staging, and prod or by some other conceptual grouping. Decrypt data using an asymmetric CryptoKey cloudkms.
google cloud kms
As a result, many organizations turn to a cloud provider's native services for encryption key management. In general, the built-in encryption is transparent to customers, but it uses Google-managed keys that aren't exportable. The permission to manage keys is cloudkms. For this example, we will copy all emails for allen-p, encrypt them, and upload them to a Cloud Storage bucket. This can be done in the using the gcloud command-line utility.