Malwarebytes command line scanner. www.littleboyblu.comab 2019-03-23
Install MalwareBytes with PowerShell
Access 18 portable tools in one place The Malwarebytes Toolset puts software like AdwCleaner, anti-bundleware, and breach remediation in one convenient place. The top rate version cannot solely control adware and malware reduction, however, has some selections being more protection collectively with an instantaneous time period scanner that routinely prevents malware and websites from infecting your computer. He is interested in finding new ways to break Windows, find common errors and help others to fix them. The other option is enter the command using a command prompt or via the Run box. As the program cannot update itself, new downloadable executables are added to the website every day with the latest definitions. Consumer remediation Malwarebytes can detect and remove Ransom.
www.littleboyblu.comGoga
Whitelist files must be text files where each line is one of the items to be excluded. It's planned to be added back in the future, but they said that back with 2. After the computer reboots and you login, you will be back at your normal desktop. Web Cureit - want way too much information from me just to download their product. Start Open the Windows prompt as administrator Start - Run - cmd.
Command Line Parameters.

Once the command prompt is open, we have to cd into to the Malwarebytes folder! The only articles I am finding are from years ago. Ignore list for both the scanner and Protection Module. It is used for reporting false positives and allows the researchers to determine why an item is being detected. Leave blank to remove any proxy settings previously set. I made a install script for MalwareBytes to do a Silent install.
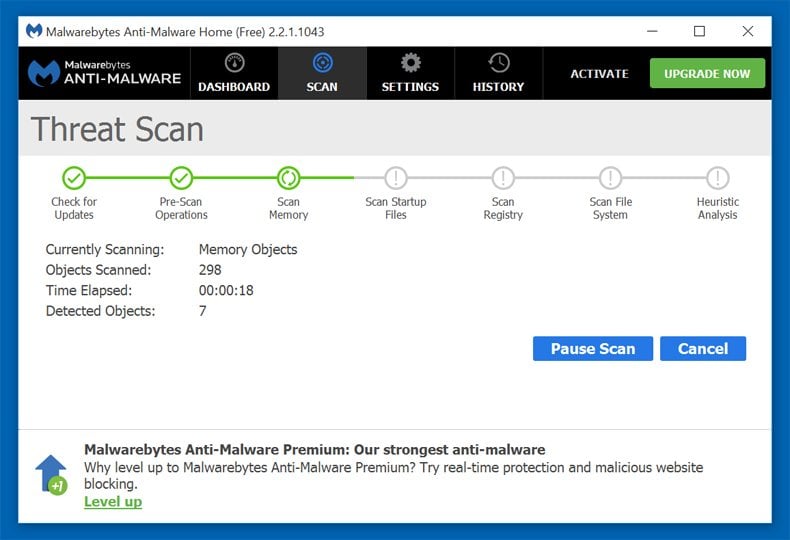
Malware Bytes command line scan
When it has finished, you be shown a message that says press any key to exit. The default is a Deep Scan with Rootkit checking enabled. The icon for this program looks like: Once you double-click on the mbar. Detected objects are saved and encrypted there so that they cannot cause further damage. I may add some of the tools listed above that don't allow drive selection.
Portable Computer/PC Repair Toolkit

Aside from that, he loves to fully customize systems with Rainmeter and Dreamscene, find out more about ancient civilizations like the Chachapoya, sharpen his digital photography skills and create software with a small group of selected developers. If you run it on a system with no internet connection select No to bypass the online definition update. How it works For system administrators, security experts, and experienced commandline users. Still a useful option if you want something extra to try. Seems a bit too specific for my purposes, but I'll keep it in mind for ransomware.
windows
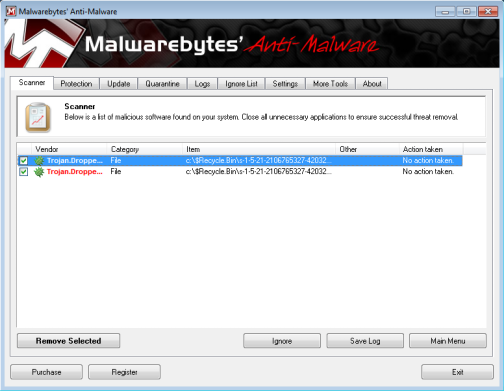
Aftermath Besides the encrypted files of the filetypes:. The results are below, listed in no particular order. Malwarebytes' Anti-Malware supports a variety of command line parameters, which can be used from either a command prompt, batch file or script. To use a command-line argument you need to append it to the command that you use to start Malwarebytes Anti-Rootkit. I want to emphasize that I'm not judging the effectiveness of any of these tools; my sole reason for testing was to find which scanners could scan user-specified drives rather than simply scan everything. I commented out the Run and WinWait commands and MouseMove worked fine. Please click on the Next button and you will then be presented with the Update Database screen.
Malwarebyte complete command line switch list
Once your computer restarts and you log back in, Windows should be operating properly again. If the path is blank, changes are reverted to default settings. You can only get your files back from backups you made before the infection happened. Malwarebytes includes some advanced command-line arguments that you can use when starting the. LockerGoga without further user interaction. If the service is not yet started or installed it is installed and started when the service parameter is run for the first time. Web are very quick with their updates as the program cannot update itself, new executables are released approximately every hour.
Portable Computer/PC Repair Toolkit
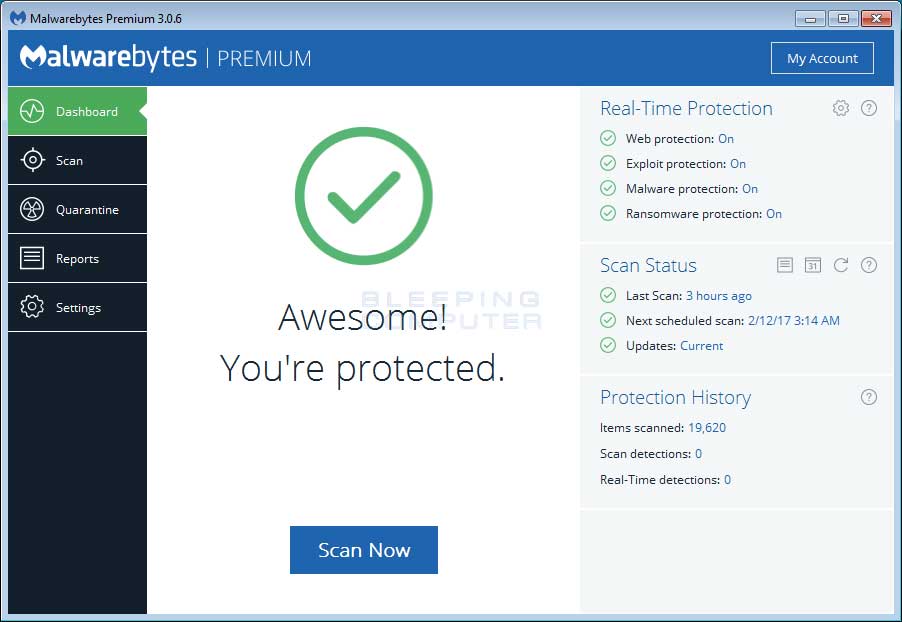
An overview of all available starting parameters is listed. Three scan types are available, Quick Scan checks the important and common areas of the system that could contain viruses, Full Scan will check the entire system and the customize option allows adding of a specific drive or folder which will be checked in addition to a Quick Scan. Or select the Threat Scan from the Scan menu. It will then recreate any missing or damaged services and repair the Layered Service Provider chain. Therefore you should only use this program if you are comfortable with using this type of software.
Malwarebytes Anti

Offsite I see this Emisoft bundle a great way to run a Malware test on a comp with no internet access. Full Scan will perform a scan of all drives on the system in addition to the Smart scan. Once you have rebooted, the detected rookits should now be removed from your computer. I replaced ControlClick with MouseMove, 444, 521and the mouse does not move. Please click on Yes button to restart your computer.