Current ccna version. Current Exam List 2019-02-25
CCNA v6.0 & CCNA1 v6.0 Exam Answer + Lab Score 100% (March 2019)
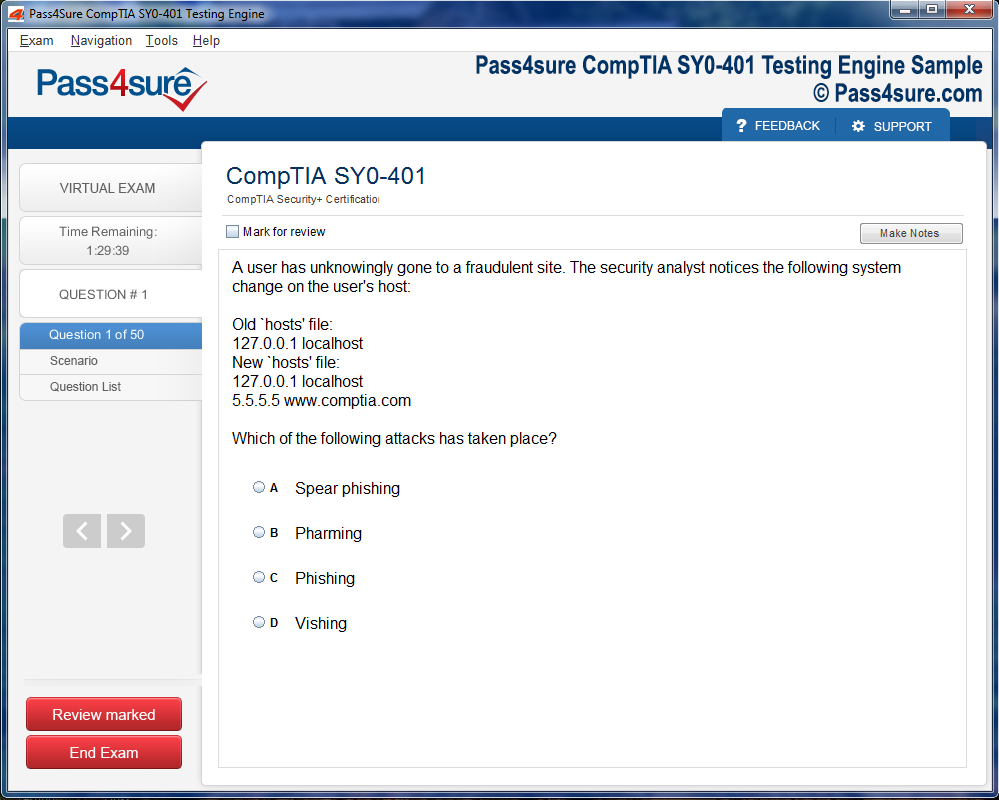
Which two messages will the client typically broadcast on the network? In short, resolving the problem means finding the root cause of the problem and fixing that problem. A benefit of anycast addressing is the capability to share load to multiple hosts. So you should review all ours exam questions and practice with our exam online systems to make sure you are clearly with the answers. The buffer size is limited to few kilobytes. If a route is not present in the routing table for a particular destination, what would the router do? Which reason for the problem is most likely true? Employers will respect this certification and the skills that you possess as a result of it all the more. Assuming that the entire network topology is shown, what is the operational status of the interfaces of R2 as indicated by the command output shown? Which three commands can you use to set a router boot image? Which command is used to know the duplex speed of serial link? Introduction In this activity, you will configure wireless computers to connect to a.
Latest Cisco CCNA Routing and Switching Certification Video Courses
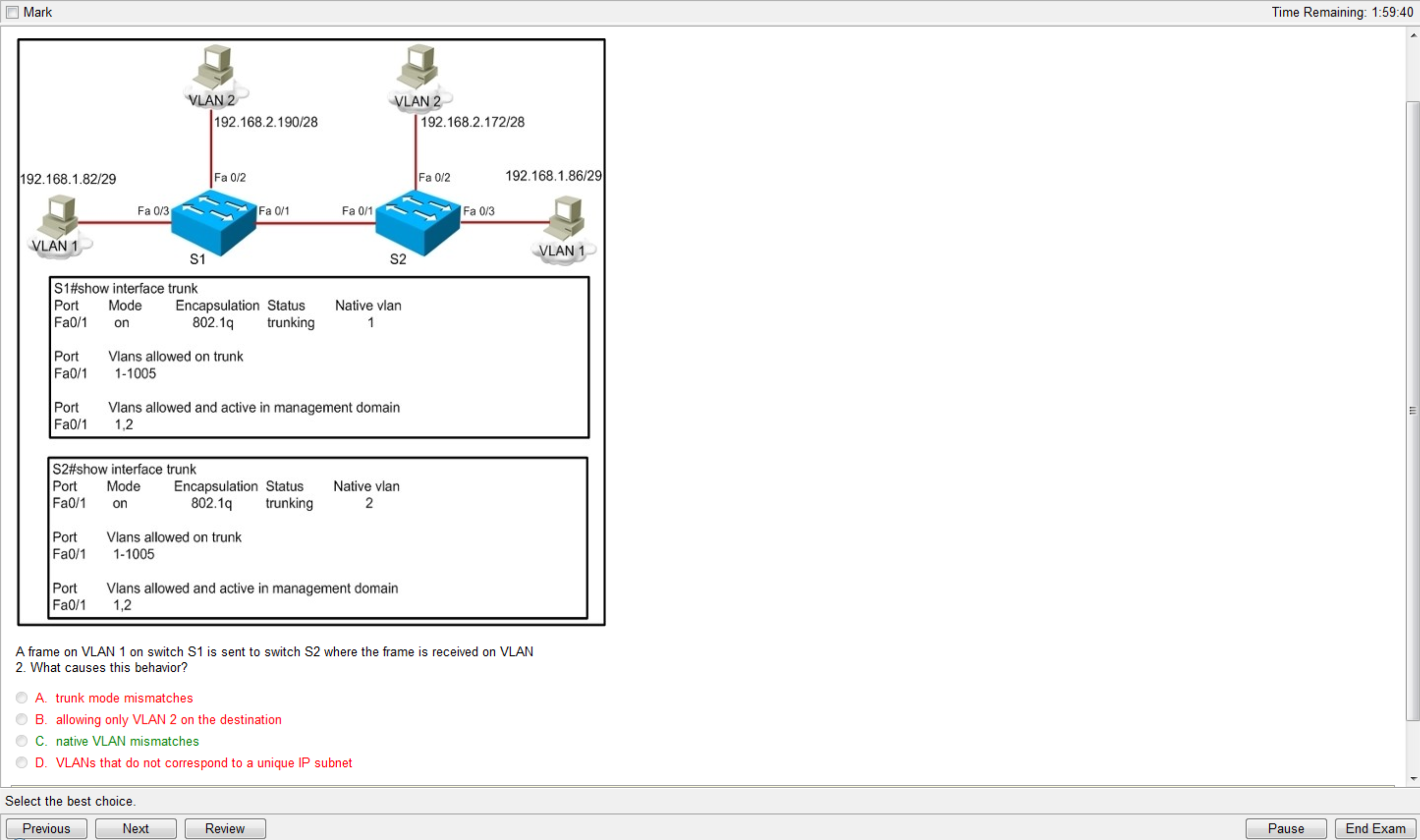
Based on the information in the graphic, what is the cause of this problem? What prompt will display after the command is issued?? Answer C is not correct as host B can ping other two hosts. What should be part of a comprehensive network security plan? What command will display the required information? Packets satisfying the match criteria for a class constitute the traffic for that class. Answer A C are two options left and they are acceptable answers. The address will not be assigned until the administrator resolves the conflict. Of course, what do you do if you cannot find the root cause, or fix resolve that root cause once found? The transport layer formats the screen so the web page appears properly no matter what device is being used to view the web site. Reference: In fact this question is not clear.
Cisco press latest ccna version trend: Cisco Press CCNA ICND Test, Cisco Press BCMSN Test, PrepLogic Cisco CCNA (640
She can access all other intranet pages. Most of students study this course. Which action will be successful? What are three message types that will be sent to the Syslog server? They are usually at least 10 times faster than analog modem connections. This number is redundant for largest corporations on the world! Which two options describe benefits of aggregated chassis technology choose 2? In which situation would the use of a static route be appropriate? We know that once you achieve it, doors should begin to open for you. The switch with lowest bridge priority value would become the root bridge. All of the interface roles of the root bridge are designated.
[SOLVED] latest CCNA version

Study training materials anywhere you want. What is the reason for this? Surely switch stacking provides redundancy as stacking creates a ring of connection with two opposite paths. Which statement about the configuration is true? Which three statements accurately describe Layer 2 Ethernet switches? The latest technologies provide a more functional approach to administrate and support for handling network security threads and also covers the security assessments on routing and switching. In the exhibit, we can recognize that the Management Workstation is in a different subnet from the SwitchB. Which two of these are characteristics of the 802.
NEW Cisco CCNA 200
Which two are advantages of static routing when compared to dynamic routing? Please note that you will not be able to use the product after it has expired if you don't renew it. The cost of leased line solutions can become significant when they are used to connect many sites over increasing distances. Three switches are connected to one another via trunk ports. Which command can you enter to set the default route for all traffic to an interface? Individual links in a bundle do not perform any hierarchical queueing. The corresponding port is put in «inconsistent» state.
What is the latest CCNA exam code for a 2018 CCNA certification?
Firebrand is an immersive environment and requires commitment. Which network addresses should be used for Link A and Network A? When talking about Hub-and-spoke we often think about the communication between Hub site and Spoke sites. By default, the priority is 100. Which three functions are performed by intermediary network devices during this conversation? But notice that console connections on a serial cable do have logging enabled by default. Courses that include certification come with a Certification Guarantee. If the current master fails, another master is elected from the stack.
Current Exam List

It drops packets to control the output rate The following diagram illustrates the key difference between traffic policing and traffic shaping. In dynamic desirable mode, the interface actively attempt to convert the link to a trunk link. Which topology provides high availability and connects some, but not all, remote sites? The lowest level is level 7. R1 show ntp status Clock is synchronized, stratum 10, reference is 10. A subnet mask is entered for the next-hop address.
CCNA v6.0 & CCNA1 v6.0 Exam Answer + Lab Score 100% (March 2019)
The result is an output rate that appears as a saw-tooth with crests and troughs. On this 7-day course, you'll also study basic network security and network device management. Therefore, you must know what to do when this type of problem is reported to you as a network problem. Once these dates are past, the Version 2 certification exams will no longer be available. It is not routable on the global Internet.
NEW Cisco CCNA 200

It supports access-level authorization for commands. When the collision is detected, they both back off and wait a random amount of time before retrying. All ports on both the switches must be set as access ports. The source interface can be configured to make routing decisions. The next hop must be directly attached to the specified output interface. Although in practical they may vary a lot.
NEW Cisco CCNA 200
Shadow rules are the rules that are never matched usually because of the first rules. What is the purpose of using these keystrokes? The default is 300 seconds. We do not make any guarantees about personal successes or benefits of obtaining certification. Answers C, D and E are wrong terminologies so they are surely not correct. In this case we call statement 1 shadows statement 2.